Question
Figure shows an authentication mechanism used by Alice to send messages to Bob. Using the message, K a and the Message Authentication Code (MAC) function
Figure shows an authentication mechanism used by Alice to send messages to Bob. Using the message, Ka and the Message Authentication Code (MAC) function h the a MAC value is calculated and sent to Bob by Alice. Consequently, Bob calculates a value and compares it with the one he received to verify if Alice sent this text.
a. Will this authentication mechanism prevent Eve to eavesdrop the message m?
b. Can Bob safely assume that Alice saw the message in question and choose to sing it?
c. Alice and Bob are concerned about the key distribution for authentication, what would be an alternate authentication mechanism to do so?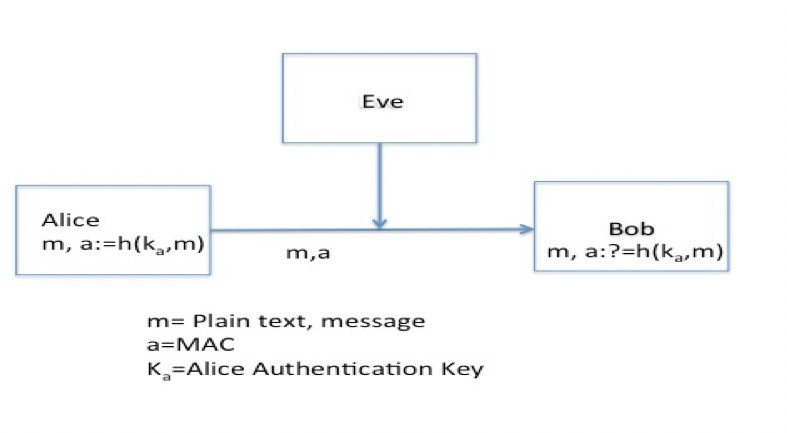
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started