Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Given below in Figure 1 is the snapshot of a tool being used to attack a victims network. 1)Name the attack in progress shown in
Given below in Figure 1 is the snapshot of a tool being used to attack a victims network.
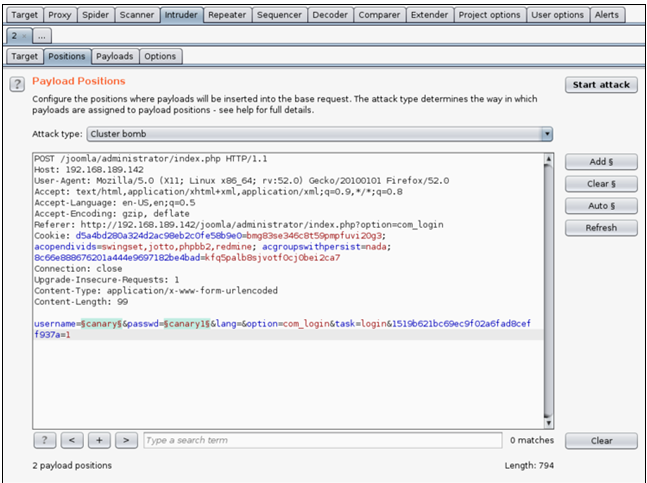
1)Name the attack in progress shown in Figure.
2) Briefly explain how the attack in Figure 1 is performed on the victims network.
3)Describe the purpose of the attack?
Configure the positions where payloads will be inserted into the base request. The attack type determines the way in which payloads are assigned to payload positions - see help for full details. Attack type: Cluster bomb ? 4 Type a search term 0 matchStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started