Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Hello, please write with full explanation when answering the questions because I will be using it for understanding and revision purposes. This regards Computer Security.
Hello, please write with full explanation when answering the questions because I will be using it for understanding and revision purposes. This regards Computer Security. Thank you.
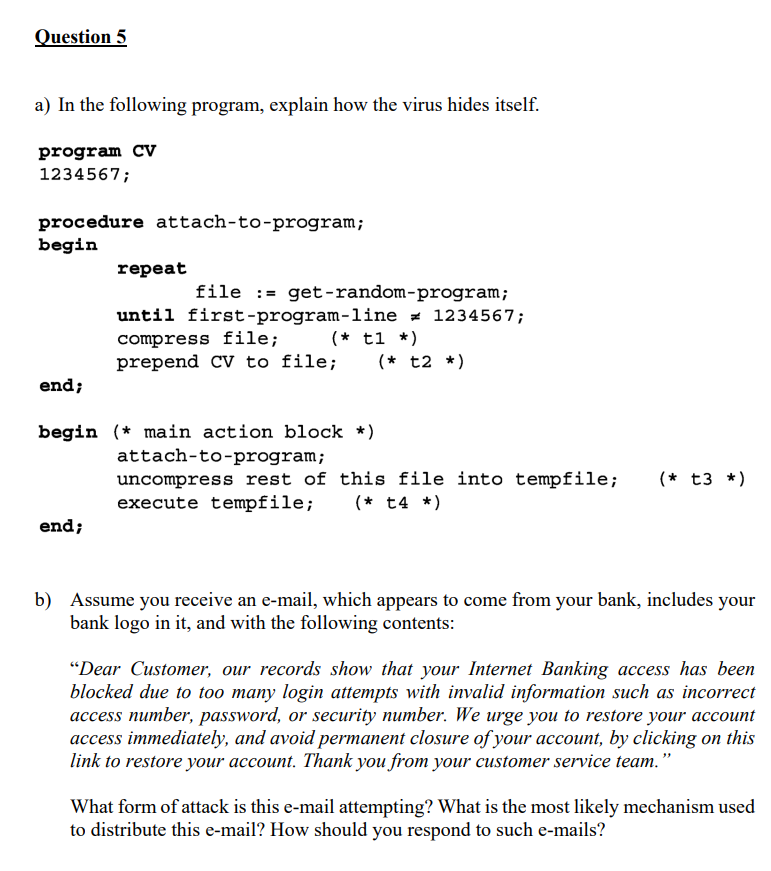
Question 5 a) In the following program, explain how the virus hides itself. b) Assume you receive an e-mail, which appears to come from your bank, includes your bank logo in it, and with the following contents: "Dear Customer, our records show that your Internet Banking access has been blocked due to too many login attempts with invalid information such as incorrect access number, password, or security number. We urge you to restore your account access immediately, and avoid permanent closure of your account, by clicking on this link to restore your account. Thank you from your customer service team." What form of attack is this e-mail attempting? What is the most likely mechanism used to distribute this e-mail? How should you respond to such e-mails
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started