Answered step by step
Verified Expert Solution
Question
1 Approved Answer
i got this question wrong. can you help me solve it. i am lost on how to solve it but going link up with a
i got this question wrong. can you help me solve it. i am lost on how to solve it but going link up with a friend to see if we can solve it lol network security
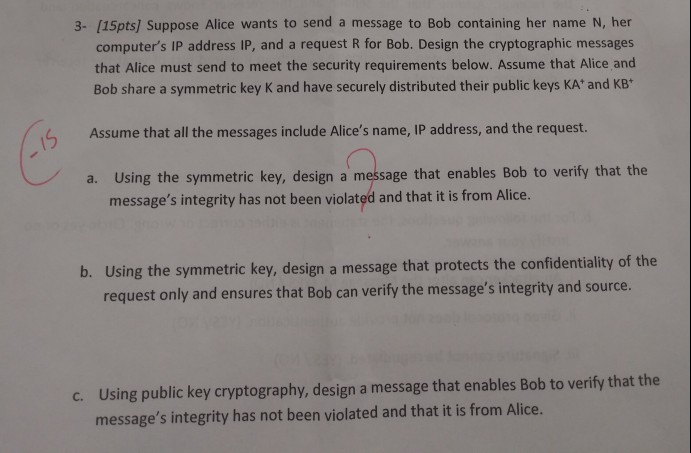
3- [15pts] Suppose Alice wants to send a message to Bob containing her name N, her computer's IP address IP, and a request R for Bob. Design the cryptographic messages that Alice must send to meet the security requirements below. Assume that Alice and Bob share a symmetric key K and have securely distributed their public keys KA' and KB* Assume that all the messages include Alice's name, IP address, and the request. a. Using the symmetric key, design a message that enables Bob to verify that the message's integrity has not been violated and that it is from Alice. Using the symmetric key, design a message that protects the confidentiality of the request only and ensures that Bob can verify the message's integrity and source b. Using public key cryptography, design a message that enables Bob to verify that the message's integrity has not been violated and that it is from Alice. cStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started