Answered step by step
Verified Expert Solution
Question
1 Approved Answer
I. Prior to the discovery of any specific public-key schemes, such as RSA, an existence proof was developed whose purpose was to demonstrate that public-key
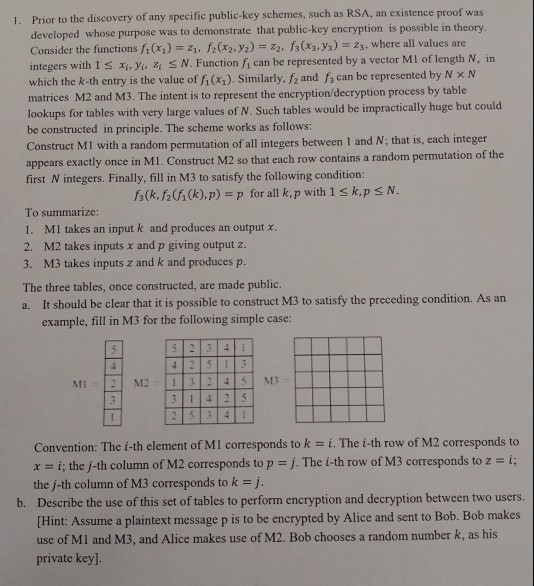
I. Prior to the discovery of any specific public-key schemes, such as RSA, an existence proof was developed whose purpose was to demonstrate that public-key encryption is possible in theory where all values are Consider the functions fi (x)1. f22.2)2. s(x.s) in tegers with 1s xi,yi Zi N. Function fi can be represented by a vector Ml of length N, in which the k-th entry is the value of fi (x) Similarly, f2 and f3 can be represented by N N matrices M2 and M3. The intent is to represent the encryption/decryption process by table lookups for tables with very large values of N. Such tables would be impractically huge but be constructed in principle. The scheme works as follows: Construct MI with a random permutation of all integers between I and N; that is, each integer appears exactly once in MI. Construct M2 so that each row contains a random permutation of the first N integers. Finally, fill in M3 to satisfy the following condition: A(k,Ah(k),p) = p for all k, p with 1 k,p N To summarize: 1. MI takes an input k and produces an output x 2. M2 takes inputs and p giving output z 3. M3 takes inputs z and k and producesp The three tables, once constructed, are made public a. It should be clear that it is possible to construct M3 to satisfy the preceding condition. As an example, fill in M3 for the following simple case Convention: The i-th element of Ml corresponds to k- i. The i-th row of M2 corresponds to x = i; the j-th column of M2 corresponds to p = j. The i-th row of M3 corresponds to z = i; the j-th column of M3 corresponds to k = j Describe the use of this set of tables to perform encryption and decryption between two users Hint: Assume a plaintext message p is to be encrypted by Alice and sent to Bob. Bob makes use of MI and M3, and Alice makes use of M2. Bob chooses a random number k, as his private key]. b
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


