Answered step by step
Verified Expert Solution
Question
1 Approved Answer
I want to solve this question with clarification.. I enclose the question and I will attach a source from the article Symmetric encryption, or secret
I want to solve this question with clarification.. I enclose the question and I will attach a source from the article
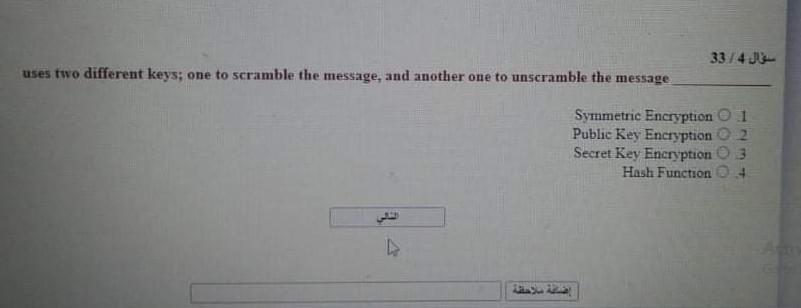
Symmetric encryption, or secret key encryption as it is usually called, uses a common key and the same cryptographic algorithm to scramble and unscramble the message as shown in Figurel. The security of the transmitted data depends on the fact that eavesdroppers with no knowledge of the key are unable to read the message. One problem with symmetric encryption is the security of the keys which must be passed from the sender to the receiver. 334 uses two different keys; one to scramble the message, and another one to unscramble the message Symmetric Encryption Public Key Encryption Secret Key Encryption Hash Function OOOO -- 2 3
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started