Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Identify / enumerate the various threats and risks in the devices and network including any interesting points relating to it with references. 2 . Investigate
Identifyenumerate the various threats and risks in the devices and network
including any interesting points relating to it with references.
Investigate and discuss the different vulnerability identified in the devices and
network.
Analyse and evaluate the techniques for protect the devices and network with
screenshots code snippets real world examples
Recommend techniques to prevent future attack on the connect devices and
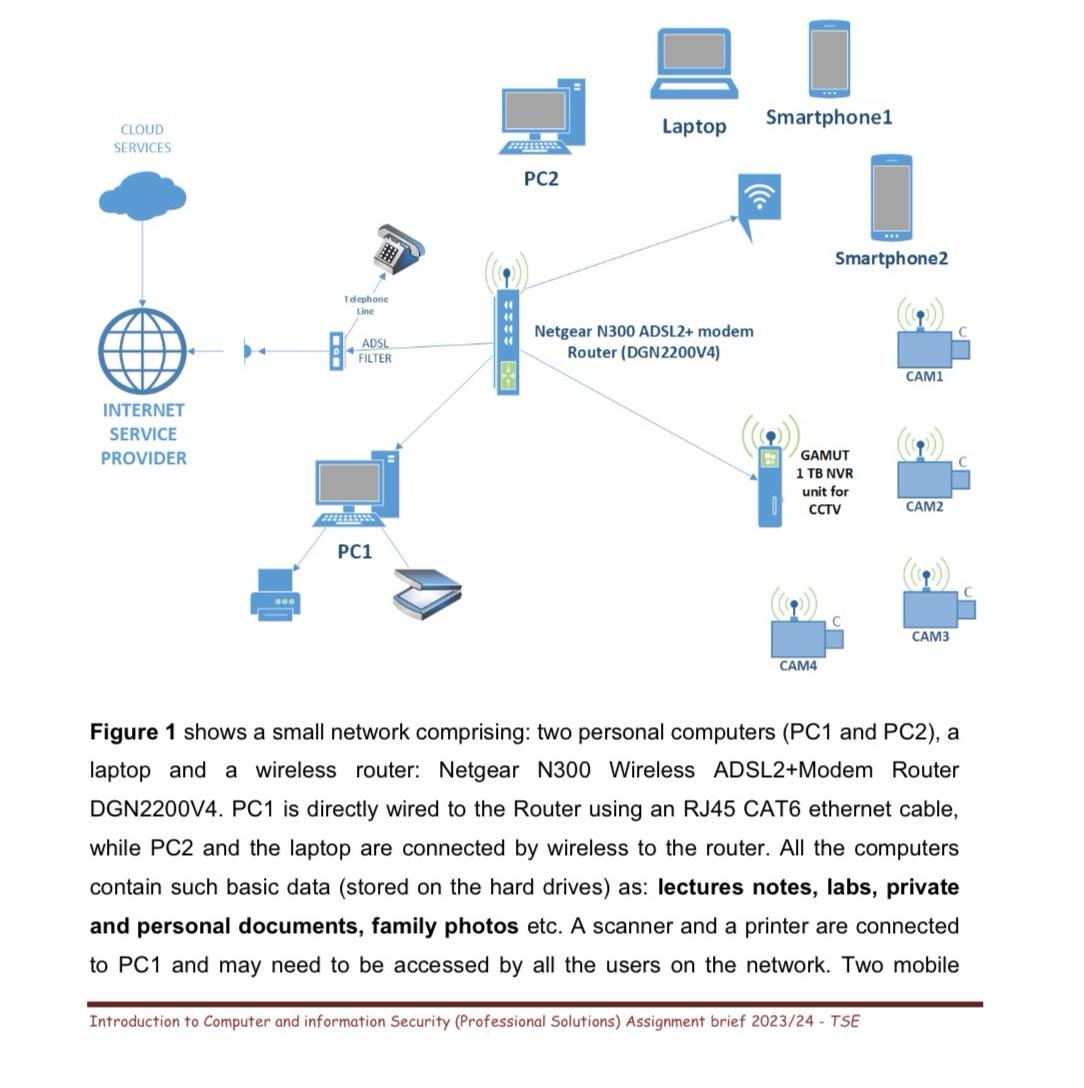
the network.Figure shows a small network comprising: two personal computers PC and PC a laptop and a wireless router: Netgear N Wireless ADSLModem Router DGNV PC is directly wired to the Router using an RJ CAT ethernet cable, while PC and the laptop are connected by wireless to the router. All the computers contain such basic data stored on the hard drives as: lectures notes, labs, private and personal documents, family photos etc. A scanner and a printer are connected to PC and may need to be accessed by all the users on the network. Two mobile
Introduction to Computer and information Security Professional Solutions Assignment brief TSE
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


