Question
Implementing an attack on Vigenre ciphers (in case the period t is unknown). Breaking the following three ciphertexts: 1. eiwemwotrnwrbpglqthnkquchtvleznwxzavfnghbmekqtvzmvjztzivvymjlivfjmurmitjyvh cuvzjgxkmpkbtvilgjgiaiadvccmpmukmgrwnyyyifqojkztvitnvbreiauzarkgxvfegtxpakfpm qaqwktmpwfjmuxvktpnibwvvyyinamrvlpglxcgcghzxgifpiaakdnaxumeyycbkinrgslqvvyct tztakutgbgvyatgbctprwxqvxvlibwvqwadfxtgoktvpipzapeivfvjtvbzqdcraivktyafikjultlace yyhmpmgegvfizqkmgfikjultizwxzbtwuwtvqdipukgrtbmfrlsxnnktgtgbugrlhhnmptpnibqq eycwbpgjsqlmywvlibvbtfbjvbqqemuxtmekpdgqkurlsvwurlrxgopcjyaewegucatjwtrrtlkpg
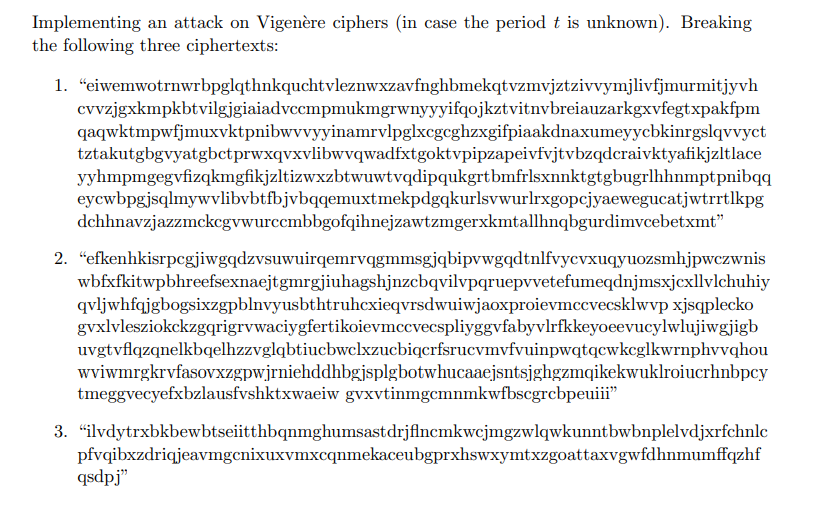
Implementing an attack on Vigenre ciphers (in case the period t is unknown). Breaking the following three ciphertexts:
1. "eiwemwotrnwrbpglqthnkquchtvleznwxzavfnghbmekqtvzmvjztzivvymjlivfjmurmitjyvh cuvzjgxkmpkbtvilgjgiaiadvccmpmukmgrwnyyyifqojkztvitnvbreiauzarkgxvfegtxpakfpm qaqwktmpwfjmuxvktpnibwvvyyinamrvlpglxcgcghzxgifpiaakdnaxumeyycbkinrgslqvvyct tztakutgbgvyatgbctprwxqvxvlibwvqwadfxtgoktvpipzapeivfvjtvbzqdcraivktyafikjultlace yyhmpmgegvfizqkmgfikjultizwxzbtwuwtvqdipukgrtbmfrlsxnnktgtgbugrlhhnmptpnibqq eycwbpgjsqlmywvlibvbtfbjvbqqemuxtmekpdgqkurlsvwurlrxgopcjyaewegucatjwtrrtlkpg dchhnavzjazzmckcgvwurccmbbgofqihnejzawtzmgerxkmtallhnqbgurdimvcebetxmt
2. "efkenhkisrpegjiwgqdzvsuwuirqemrvqgmmsgjqbipvwgqdtnlfvycvxuqyuozsmhjpwczwnis wbfxfkitwpbhreefsexnaejtgmrgjiuhagshjnzcbqvilvpqruepvvetefumeqdnjmsxjcxllvlchuhiy qvljwhfqjgbogsixzgpblnvyusbthtruhexieqvrsdwuiwjaoxproievmccvecsklwvp xjsqplecko gvxlvlesziokckzgqrigrywaciygfertikoievmccvecspliyggvfabyvlrfkkeyoeevucylwlujiwgjigb uvgtvflqzqnelkbqelhzzvglqbtiucbwclxzucbiqcrfsrucvmvfvuinpwqtqcwkcglkwrnphvvqhou wviwmrgkrvfasovxzgpwjrniehddhbgjsplgbotwhucaaejsntsjghgzmqikekwuklroiucrhnbpcy tmeggvecyefxbzlausfvshktxwaeiw gvxvtinmgcmnmkwfbscgrcbpeuiii"
3. "ilvdytrxbkbewbtseiitthbqnmghumsastdrjfincmkwcjmgzwlqwkunntbwbnplelvdjxrfchnlc pfvqibxzdriqjeavmgenixuxvmxcqnmekaceubgprxhswxymtxzgoattaxvgwfdhnmumffqzhf qsdpj
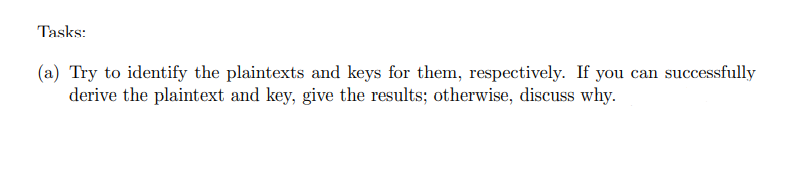
Tasks:
(a) Try to identify the plaintexts and keys for them, respectively. If you can successfully derive the plaintext and key, give the results; otherwise, discuss why.
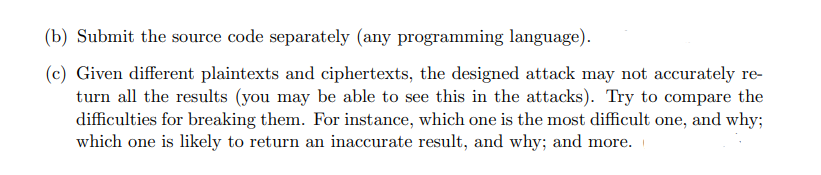
(b) Submit the source code separately (any programming language).
(c) Given different plaintexts and ciphertexts, the designed attack may not accurately re- turn all the results (you may be able to see this in the attacks). Try to compare the difficulties for breaking them. For instance, which one is the most difficult one, and why; which one is likely to return an inaccurate result, and why; and more.
Implementing an attack on Vigenre ciphers (in case the period t is unknown). Breaking the following three ciphertexts: 1. "eiwemwotrnwrbpglqthnkquchtvleznwxzavfnghbmekqtvzmvjztzivvymjlivfjmurmitjyvh cvvzjgxkmpkbtvilgjgiaiadvccmpmukmgrwnyyyifqojkztvitnvbreiauzarkgxvfegtxpakfpm qaqwktmpwfjmuxvktpnibwvvyyinamrvlpglxcgcghzxgifpiaakdnaxumeyycbkinrgslqvvyct tztakutgbgvyatgbctprwxqvxvlibwvqwadfxtgoktvpipzapeivfvjtvbzqdcraivktyafikjzltlace yyhmpmgegvfizqkmgfikjzltizwxzbtwuwtvqdipqukgrtbmfrlsxnnktgtgbugrlhhnmptpnibqq eycwbpgjsqlmywvlibvbtfbjvbqqemuxtmekpdgqkurlsvwurlrxgopcjyaewegucatjwtrrtlkpg dchhnavzjazzmckcgvwurccmbbgofqihnejzawtzmgerxkmtallhnqbgurdimvcebetxmt" 2. "efkenhkisrpcgjiwgqdzvsuwuirqemrvqgmmsgjqbipvwgqdtnlfvycvxuqyuozsmhjpwczwnis wbfxfkitwpbhreefsexnaejtgmrgjiuhagshjnzcbqvilvpqruepvvetefumeqdnjmsxjcxllvlchuhiy qvljwhfqjgbogsixzgpblnvyusbthtruhcxieqvrsdwuiwjaoxproievmccvecsklwvp xjsqplecko gvxlvlesziokckzgqrigrywaciygfertikoievmccvecspliyggvfabyvlrfkkeyoeevucylwlujiwgjigb uvgtvfiqzqnelkbqelhzzvglqbtiucbwclxzucbiqcrfsrucvmvfvuinpwqtqcwkcglkwrnphyvqhou wviwmrgkrvfasovxzgpwjrniehddhbgjsplgbotwhucaaejsntsjghgzmqikekwuklroiucrhnbpcy tmeggvecyefxbzlausfvshktxwaeiw gvxvtinmgcmnmkwfbscgrcbpeuiii" 3. "vdytrxbkbewbtseiitthbqnmghumsastdrjfincmkwejmgzwlqwkunntbwbnplelvdjxrfchnlc pfvqibxzdriqjeavmgenixuxvmxcqnmekaceubgprxhswxymtxzgoattaxvgwfdhnmumffqzhf qsdpj" Tasks: (a) Try to identify the plaintexts and keys for them, respectively. If you can successfully derive the plaintext and key, give the results; otherwise, discuss why. (b) Submit the source code separately (any programming language). (c) Given different plaintexts and ciphertexts, the designed attack may not accurately re- turn all the results (you may be able to see this in the attacks). Try to compare the difficulties for breaking them. For instance, which one is the most difficult one, and why; which one is likely to return an inaccurate result, and why; and more. Implementing an attack on Vigenre ciphers (in case the period t is unknown). Breaking the following three ciphertexts: 1. "eiwemwotrnwrbpglqthnkquchtvleznwxzavfnghbmekqtvzmvjztzivvymjlivfjmurmitjyvh cvvzjgxkmpkbtvilgjgiaiadvccmpmukmgrwnyyyifqojkztvitnvbreiauzarkgxvfegtxpakfpm qaqwktmpwfjmuxvktpnibwvvyyinamrvlpglxcgcghzxgifpiaakdnaxumeyycbkinrgslqvvyct tztakutgbgvyatgbctprwxqvxvlibwvqwadfxtgoktvpipzapeivfvjtvbzqdcraivktyafikjzltlace yyhmpmgegvfizqkmgfikjzltizwxzbtwuwtvqdipqukgrtbmfrlsxnnktgtgbugrlhhnmptpnibqq eycwbpgjsqlmywvlibvbtfbjvbqqemuxtmekpdgqkurlsvwurlrxgopcjyaewegucatjwtrrtlkpg dchhnavzjazzmckcgvwurccmbbgofqihnejzawtzmgerxkmtallhnqbgurdimvcebetxmt" 2. "efkenhkisrpcgjiwgqdzvsuwuirqemrvqgmmsgjqbipvwgqdtnlfvycvxuqyuozsmhjpwczwnis wbfxfkitwpbhreefsexnaejtgmrgjiuhagshjnzcbqvilvpqruepvvetefumeqdnjmsxjcxllvlchuhiy qvljwhfqjgbogsixzgpblnvyusbthtruhcxieqvrsdwuiwjaoxproievmccvecsklwvp xjsqplecko gvxlvlesziokckzgqrigrywaciygfertikoievmccvecspliyggvfabyvlrfkkeyoeevucylwlujiwgjigb uvgtvfiqzqnelkbqelhzzvglqbtiucbwclxzucbiqcrfsrucvmvfvuinpwqtqcwkcglkwrnphyvqhou wviwmrgkrvfasovxzgpwjrniehddhbgjsplgbotwhucaaejsntsjghgzmqikekwuklroiucrhnbpcy tmeggvecyefxbzlausfvshktxwaeiw gvxvtinmgcmnmkwfbscgrcbpeuiii" 3. "vdytrxbkbewbtseiitthbqnmghumsastdrjfincmkwejmgzwlqwkunntbwbnplelvdjxrfchnlc pfvqibxzdriqjeavmgenixuxvmxcqnmekaceubgprxhswxymtxzgoattaxvgwfdhnmumffqzhf qsdpj" Tasks: (a) Try to identify the plaintexts and keys for them, respectively. If you can successfully derive the plaintext and key, give the results; otherwise, discuss why. (b) Submit the source code separately (any programming language). (c) Given different plaintexts and ciphertexts, the designed attack may not accurately re- turn all the results (you may be able to see this in the attacks). Try to compare the difficulties for breaking them. For instance, which one is the most difficult one, and why; which one is likely to return an inaccurate result, and why; and more
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started