Question
In addition to stack-based buffer overflow attacks, heap overflows can also be exploited. Consider the following C code, which illustrates a heap overflow. (a) Compile
In addition to stack-based buffer overflow attacks, heap overflows can also be exploited. Consider the following C code, which illustrates a heap overflow.
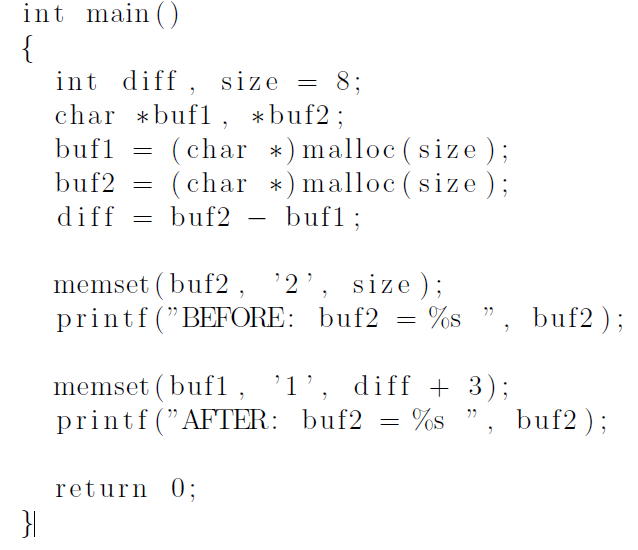
(a) Compile and execute this program. What is printed?
(b) Explain the results you obtained in part a.
(c) In terms of C/C++ memory management, what is the difference between stack and heap? In particular, which one is allocated/deallocated automatically, and which one needs programmers to take care of?
(d) Explain how a heap-based buffer overflow works, in contrast to the stackbased buffer overflow.
= int main() { int diff, size 8; char *bufl, *buf2 ; buf1 (char *) malloc(size); buf2 (char *) malloc(size ); diff buf2 bufl; = = = memset (buf2, '2', size ); printf("BEFORE: buf2 %s", buf2 ); memset (bufi, 'l', diff + 3); printf("AFTER: buf2 %s", buf2); = return 0; }Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started