Question
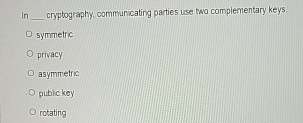
In cryptography, communicating parties use two complementary keys. symmetric privacy asymmetric pubickey rotating
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get StartedRecommended Textbook for
Database Systems For Advanced Applications 17th International Conference Dasfaa 2012 International Workshops Flashdb Items Snsm Sim Dqdi Busan South Korea April 2012 Proceedings Lncs 7240
Authors: Hwanjo Yu ,Ge Yu ,Wynne Hsu ,Yang-Sae Moon ,Rainer Unland ,Jaesoo Yoo
2012th Edition
Students also viewed these Databases questions
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Study smarter with the SolutionInn App



