Question: In this problem, we explore attacks on linear ciphers as given in (2). a. (3 marks) If each key matrix K is chosen equally likely,
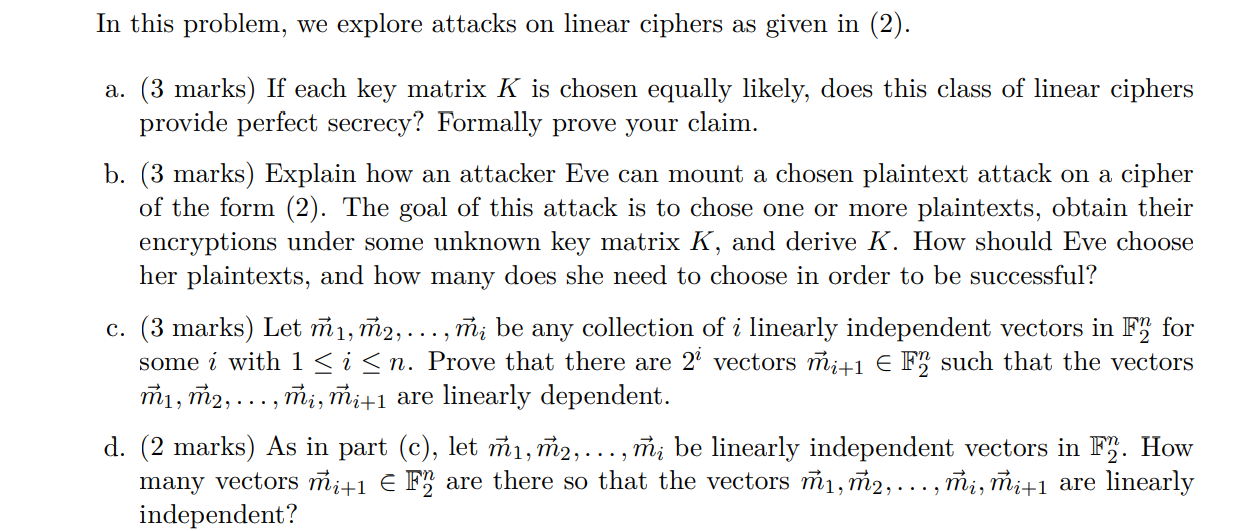
In this problem, we explore attacks on linear ciphers as given in (2). a. (3 marks) If each key matrix K is chosen equally likely, does this class of linear ciphers provide perfect secrecy? Formally prove your claim. b. (3 marks) Explain how an attacker Eve can mount a chosen plaintext attack on a cipher of the form (2). The goal of this attack is to chose one or more plaintexts, obtain their encryptions under some unknown key matrix K, and derive K. How should Eve choose her plaintexts, and how many does she need to choose in order to be successful? c. (3 marks) Let , m2, ..., mi be any collection of i linearly independent vectors in F for some i with 1
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


