Answered step by step
Verified Expert Solution
Question
1 Approved Answer
information security Consider the code in Table 11.5, which is susceptible to a linearization attack. Suppose that we modify the program as follows: Note that
information security
Consider the code in Table 11.5, which is susceptible to a linearization attack. Suppose that we modify the program as follows:
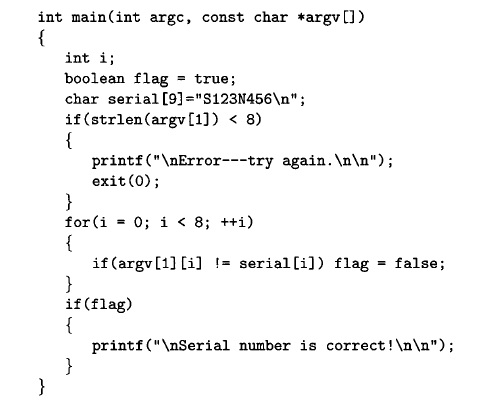
Note that we never break out of the for loop early, yet we can still determine whether the correct serial number was entered. Explain why this modified version of the program is still susceptible to a linearization attack.
int main(int argc, const char *argv []) int i; boolean flag - true; char serial [9]-"S123N456 "; if(strlen(argv[1])
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started