Answered step by step
Verified Expert Solution
Question
1 Approved Answer
John, a threat actor, called up Johana, the IT help desk member of the targeted organization, and informed her that Mr . Tibiyani was about
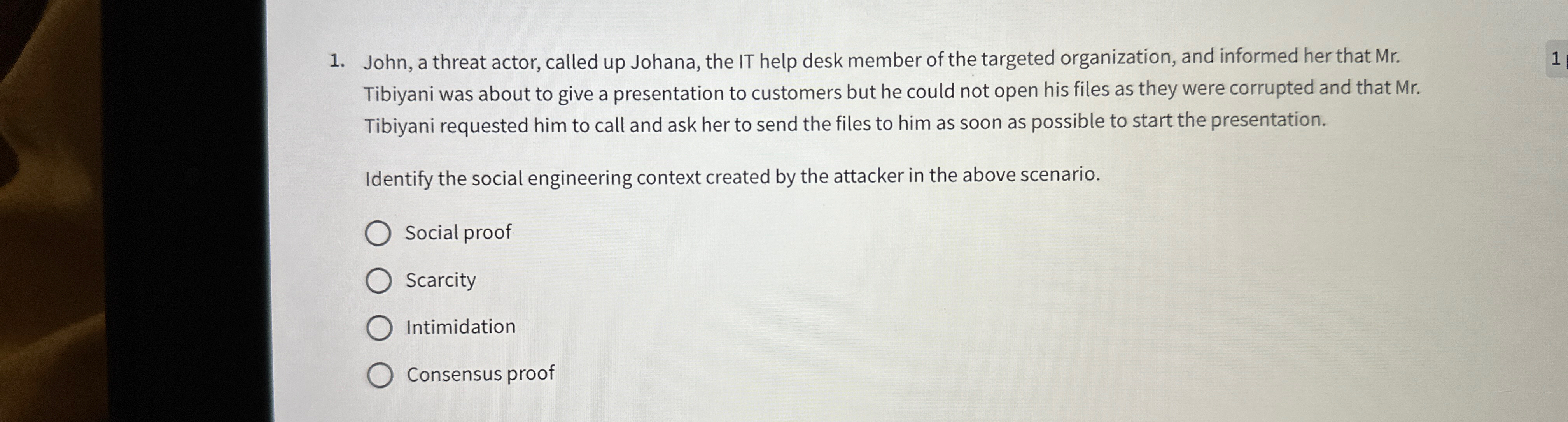
John, a threat actor, called up Johana, the IT help desk member of the targeted organization, and informed her that Mr Tibiyani was about to give a presentation to customers but he could not open his files as they were corrupted and that Mr Tibiyani requested him to call and ask her to send the files to him as soon as possible to start the presentation.
Identify the social engineering context created by the attacker in the above scenario.
Social proof
Scarcity
Intimidation
Consensus proof
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


