Answered step by step
Verified Expert Solution
Question
1 Approved Answer
John keeps a list on his cell phone of all the passwords he uses to access different websites. However, he does not write the
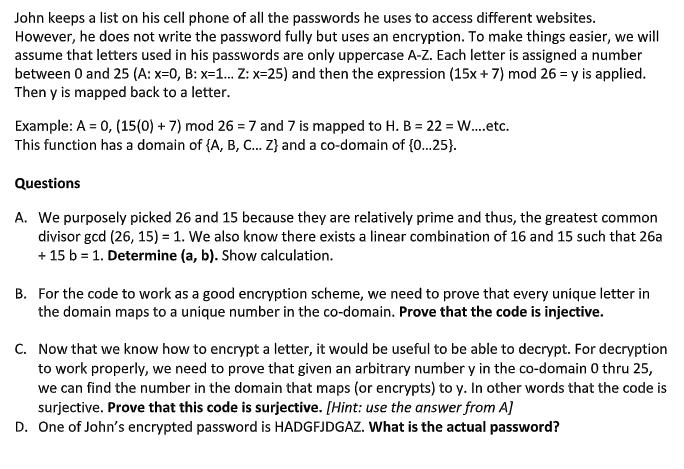
John keeps a list on his cell phone of all the passwords he uses to access different websites. However, he does not write the password fully but uses an encryption. To make things easier, we will assume that letters used in his passwords are only uppercase A-Z. Each letter is assigned a number between 0 and 25 (A: x=0, B: x=1... Z: x=25) and then the expression (15x+7) mod 26 = y is applied. Then y is mapped back to a letter. Example: A = 0, (15(0) + 7) mod 267 and 7 is mapped to H. B = 22 = W....etc. This function has a domain of {A, B, C... Z} and a co-domain of {0...25}. Questions A. We purposely picked 26 and 15 because they are relatively prime and thus, the greatest common divisor gcd (26, 15) = 1. We also know there exists a linear combination of 16 and 15 such that 26a + 15 b = 1. Determine (a, b). Show calculation. B. For the code to work as a good encryption scheme, we need to prove that every unique letter in the domain maps to a unique number in the co-domain. Prove that the code is injective. C. Now that we know how to encrypt a letter, it would be useful to be able to decrypt. For decryption to work properly, we need to prove that given an arbitrary number y in the co-domain 0 thru 25, we can find the number in the domain that maps (or encrypts) to y. In other words that the code is surjective. Prove that this code is surjective. [Hint: use the answer from A] D. One of John's encrypted password is HADGFJDGAZ. What is the actual password?
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started