Answered step by step
Verified Expert Solution
Question
1 Approved Answer
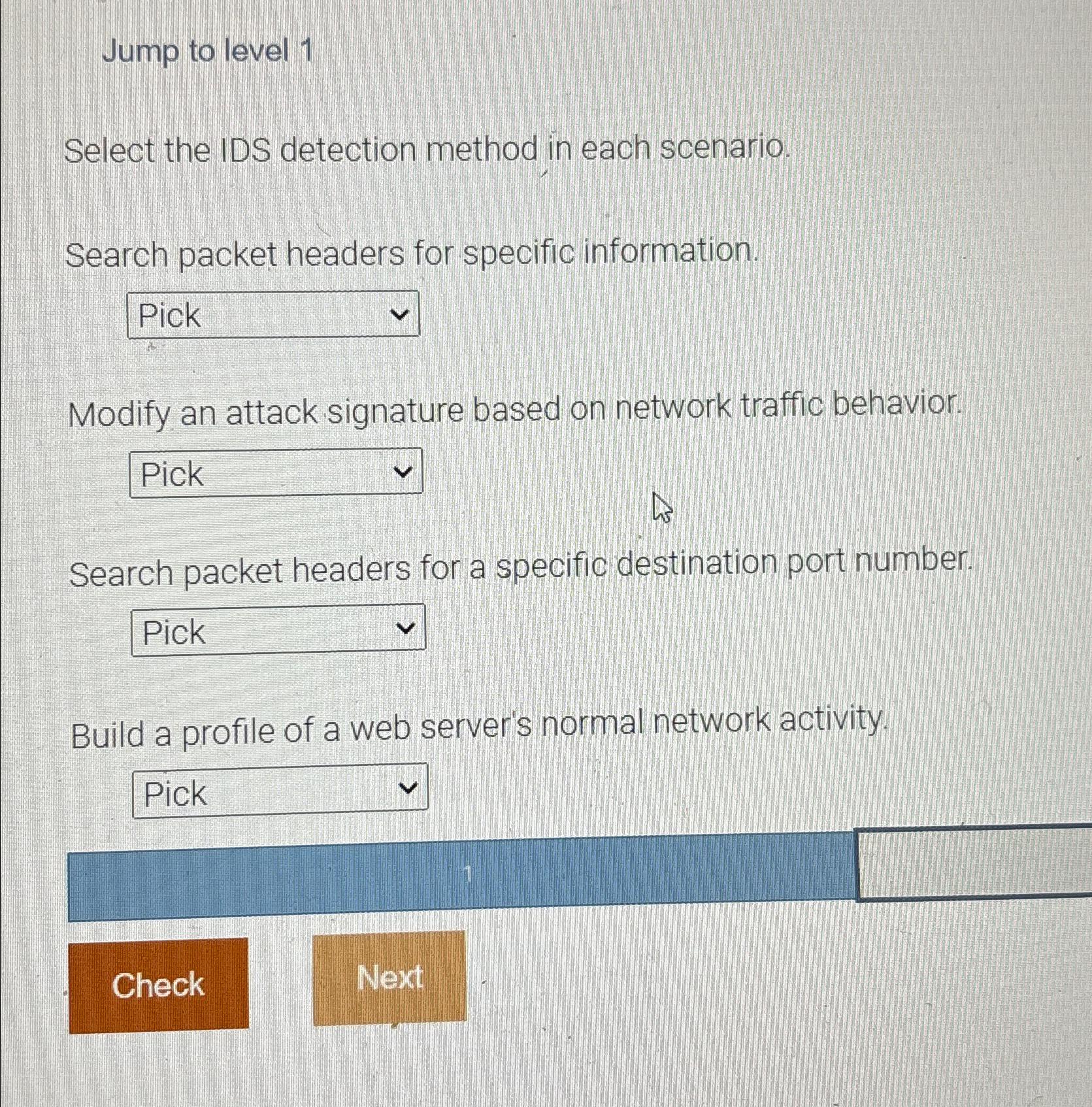
Jump to level 1 Select the IDS detection method in each scenario. Search packet headers for specific information. Modify an attack signature based on network
Jump to level
Select the IDS detection method in each scenario.
Search packet headers for specific information.
Modify an attack signature based on network traffic behavior.
Search packet headers for a specific destination port number.
Build a profile of a web server's normal network activity.
Check
Next
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started