Question: Match the description to the best fitting term: ethical hacking for example computer security experts and testing specialists who focus on penetration and related testing
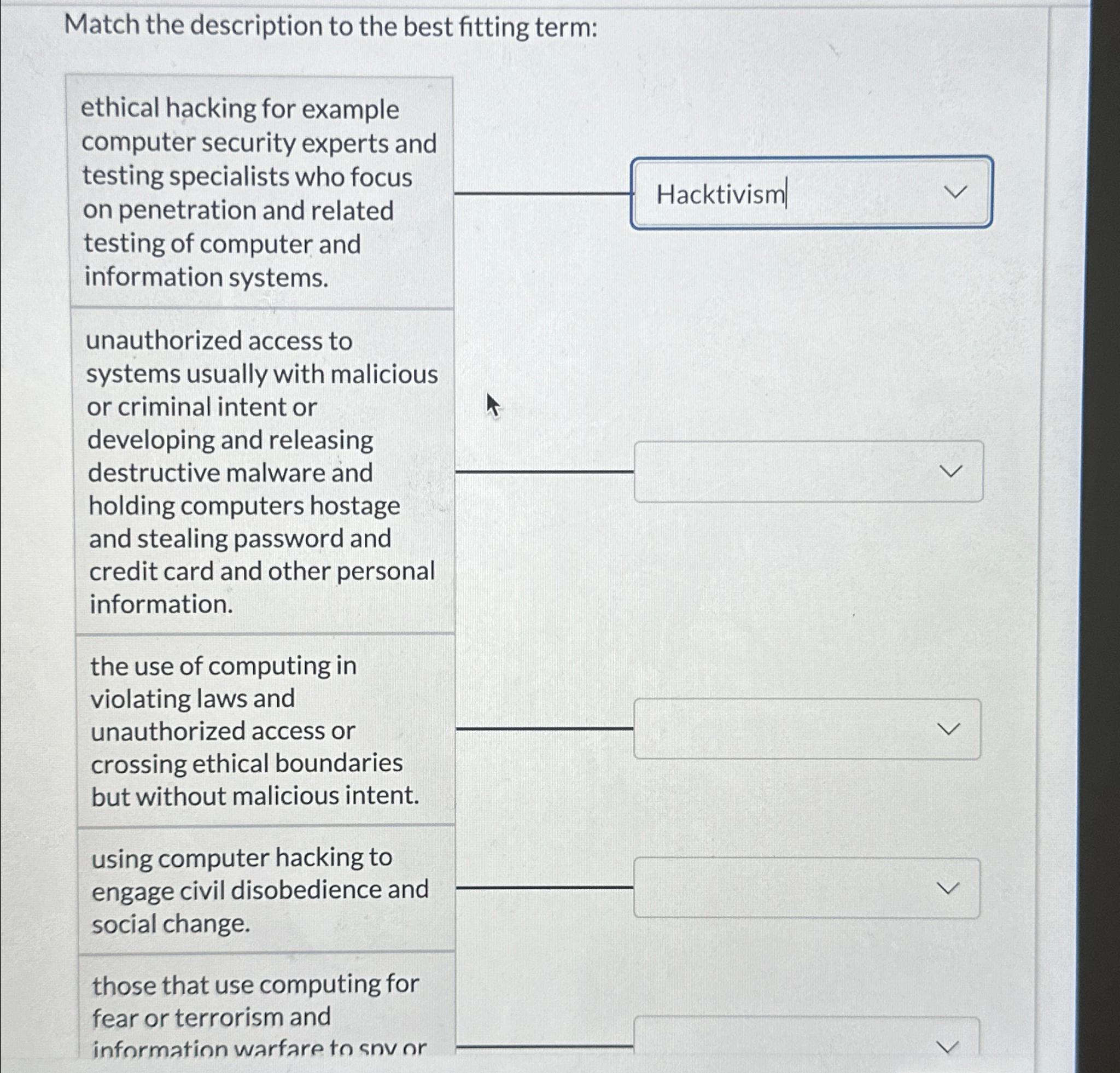
Match the description to the best fitting term:
ethical hacking for example computer security experts and testing specialists who focus on penetration and related testing of computer and information systems.
unauthorized access to systems usually with malicious or criminal intent or developing and releasing destructive malware and holding computers hostage and stealing password and credit card and other personal information.
the use of computing in violating laws and unauthorized access or crossing ethical boundaries but without malicious intent.
using computer hacking to engage civil disobedience and social change.
those that use computing for fear or terrorism and information warfare to snv or
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


