Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Message integrity can be bypassed if an attacker captures a message in transit, modifies it and then generates a new hash. Since hashing algorithms are
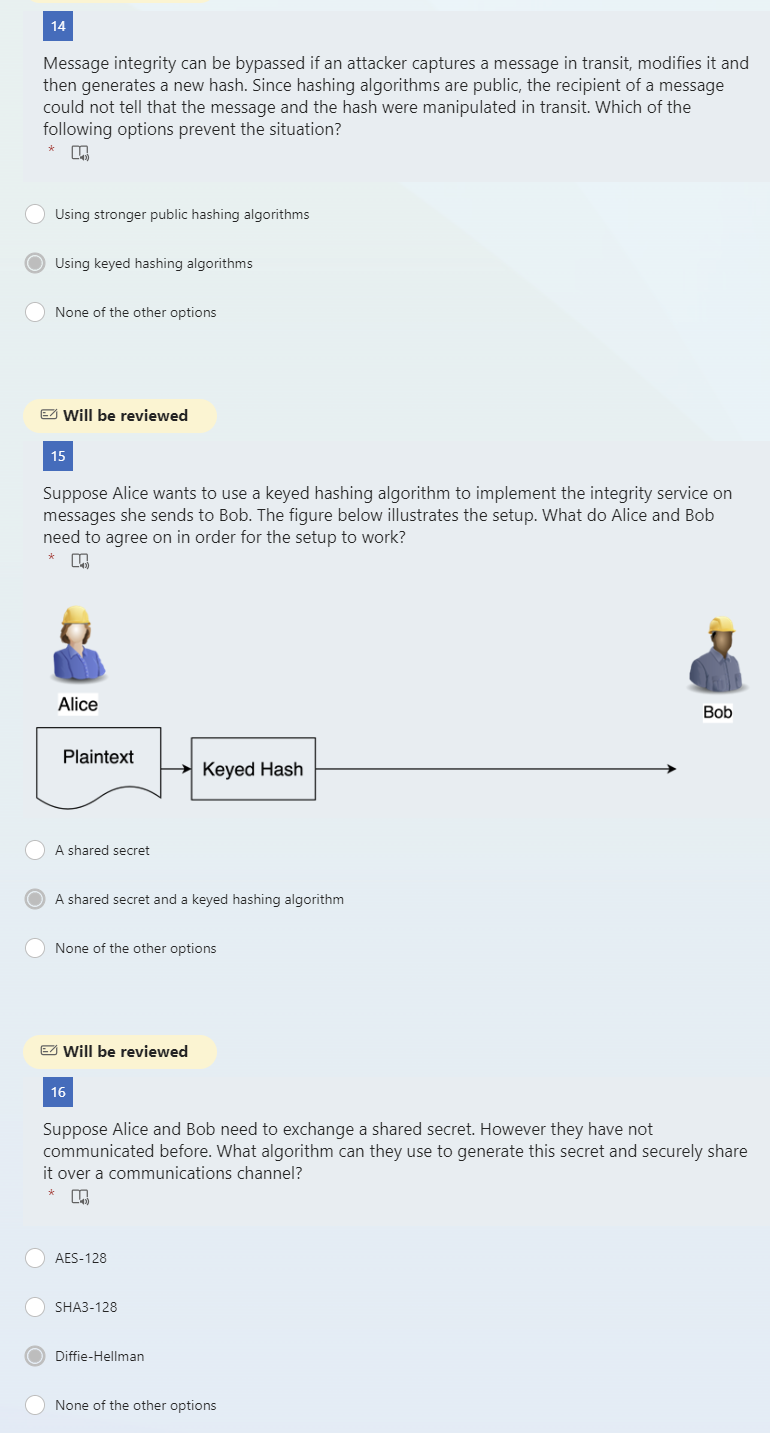
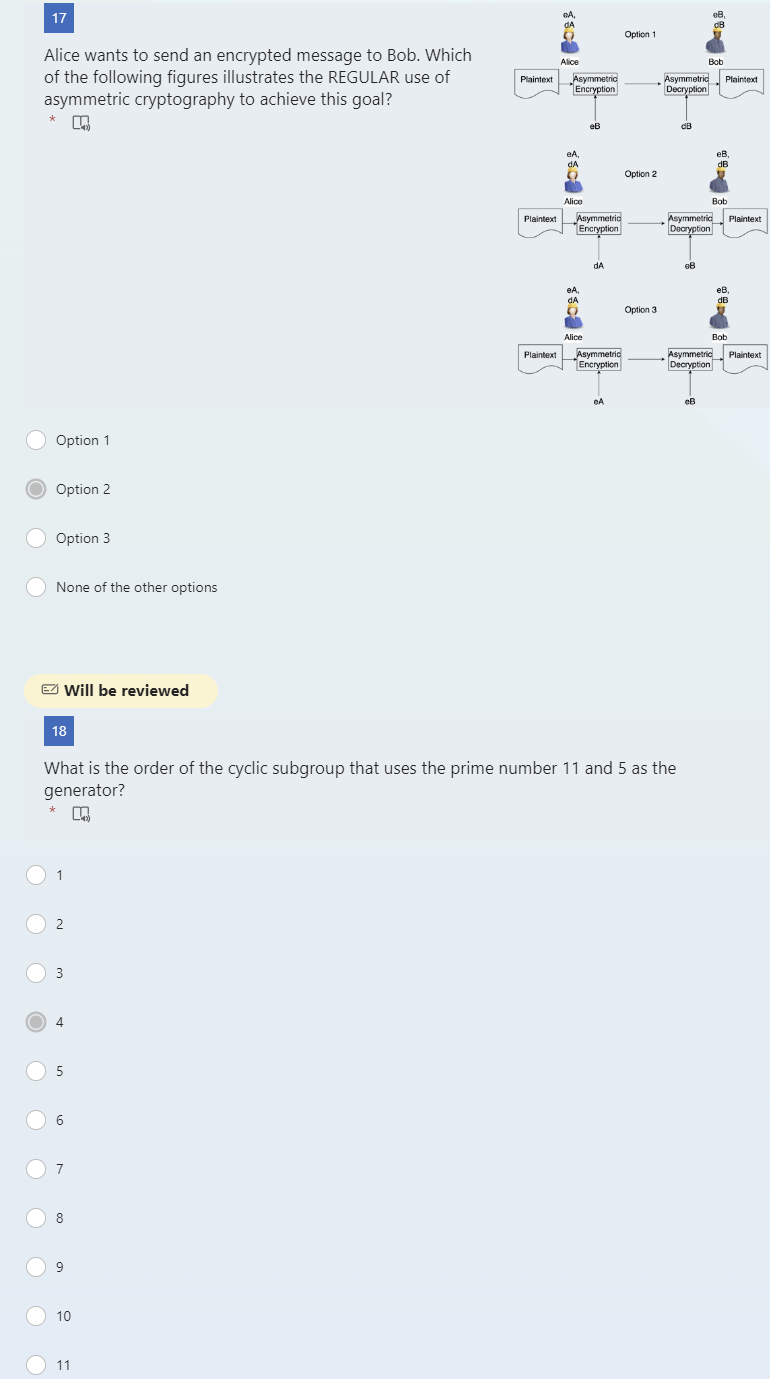 Message integrity can be bypassed if an attacker captures a message in transit, modifies it and then generates a new hash. Since hashing algorithms are public, the recipient of a message could not tell that the message and the hash were manipulated in transit. Which of the following options prevent the situation? Using stronger public hashing algorithms Using keyed hashing algorithms None of the other options 15 Suppose Alice wants to use a keyed hashing algorithm to implement the integrity service on messages she sends to Bob. The figure below illustrates the setup. What do Alice and Bob need to agree on in order for the setup to work? A shared secret A shared secret and a keyed hashing algorithm None of the other options 16 Suppose Alice and Bob need to exchange a shared secret. However they have not communicated before. What algorithm can they use to generate this secret and securely share it over a communications channel? AES-128 SHA3-128 Diffie-Hellman None of the other options Alice wants to send an encrypted message to Bob. Which of the following figures illustrates the REGULAR use of asymmetric cryptography to achieve this goal? Option 1 Option 2 Option 3 None of the other options Will be reviewed 18 What is the order of the cyclic subgroup that uses the prime number 11 and 5 as the generator? 1 2 3 4 5 6 7 8 9 10 11
Message integrity can be bypassed if an attacker captures a message in transit, modifies it and then generates a new hash. Since hashing algorithms are public, the recipient of a message could not tell that the message and the hash were manipulated in transit. Which of the following options prevent the situation? Using stronger public hashing algorithms Using keyed hashing algorithms None of the other options 15 Suppose Alice wants to use a keyed hashing algorithm to implement the integrity service on messages she sends to Bob. The figure below illustrates the setup. What do Alice and Bob need to agree on in order for the setup to work? A shared secret A shared secret and a keyed hashing algorithm None of the other options 16 Suppose Alice and Bob need to exchange a shared secret. However they have not communicated before. What algorithm can they use to generate this secret and securely share it over a communications channel? AES-128 SHA3-128 Diffie-Hellman None of the other options Alice wants to send an encrypted message to Bob. Which of the following figures illustrates the REGULAR use of asymmetric cryptography to achieve this goal? Option 1 Option 2 Option 3 None of the other options Will be reviewed 18 What is the order of the cyclic subgroup that uses the prime number 11 and 5 as the generator? 1 2 3 4 5 6 7 8 9 10 11 Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started