Miller Harrison was still working his way through his attack protocol.
Nmap started out as it usually did, by giving the program identification and version number. Then it started reporting back on the first host in the SLS network. It reported all of the open ports on this server. The program moved on to a second host and began reporting back the open ports on that system, too. Once it reached the third host, however, it suddenly stopped.
Miller restarted Nmap, using the last host IP as the starting point for the next scan. No response. He opened another command window and tried to ping the first host he had just port-scanned. No luck. He tried to ping the SLS firewall. Nothing. He happened to know the IP address for the SLS edge router. He pinged that and got the same result. He had been blackholed, meaning his IP address had been put on a list of addresses from which the SLS edge router would no longer accept packets. Ironically, the list was his own doing. The IDPS he had been helping SLS configure seemed to be working just fine at the moment. His attempt to hack the SLS network was shut down cold.
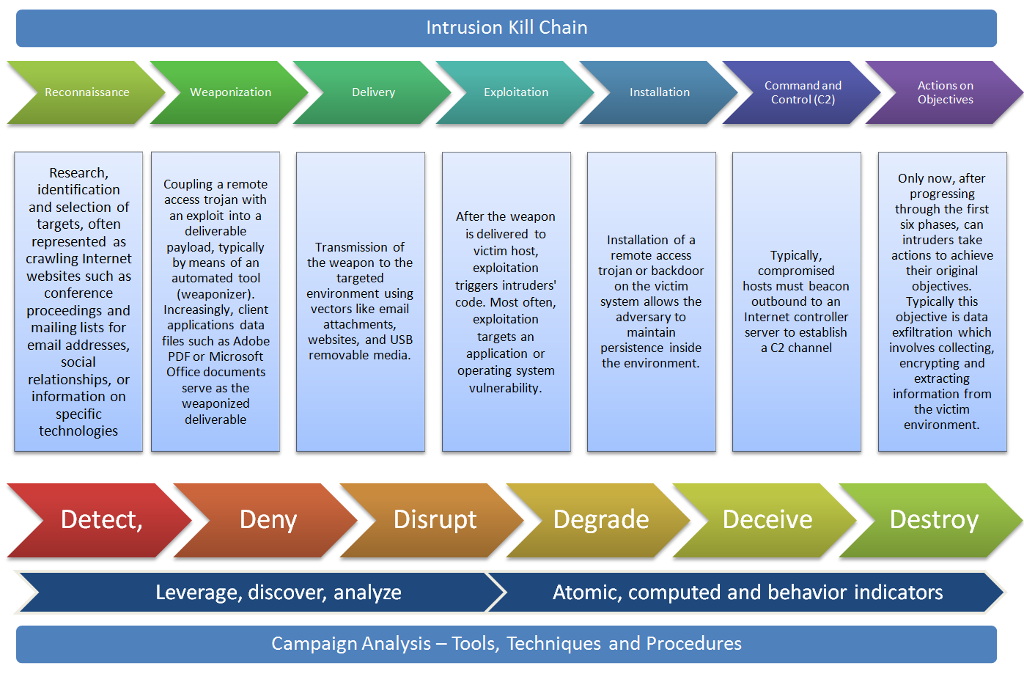
Consider Millers hacking attempt in light of the intrusion kill chain described earlier and shown in figure below. At which phase in the kill chain has SLS countered his vendetta?
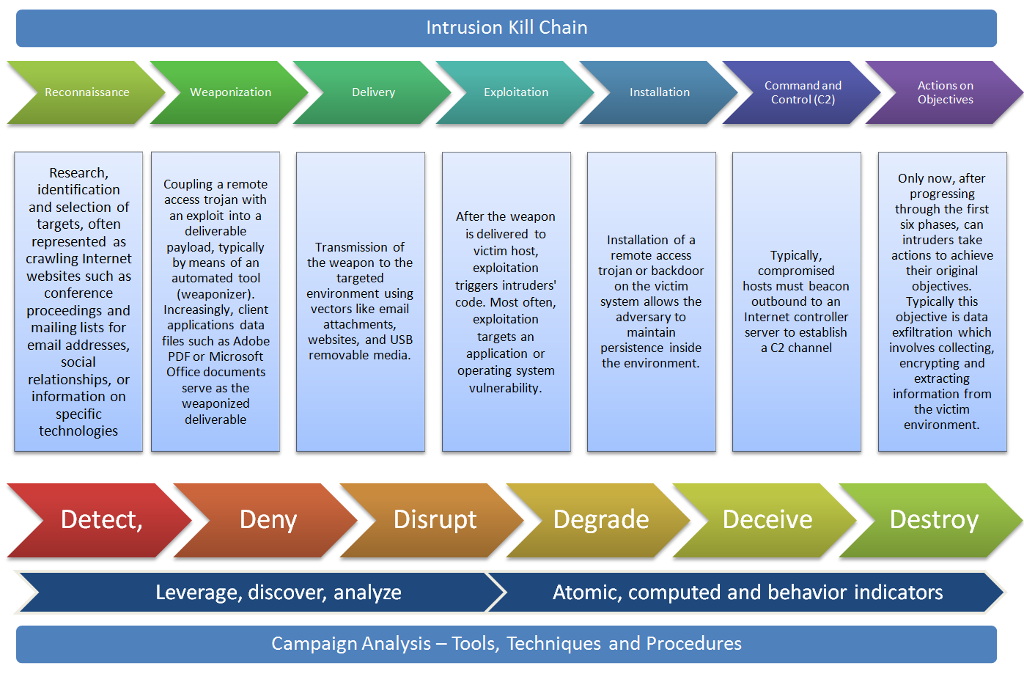
Intrusion Kill Chain Actions on Reconnaissance Weaponization Delivery Exploitation Installation Control (C2) Research, Only now, after progressing through the first six phases, can intruders take actions to achieve their original identificationCoupling a remote an exploit into a After the weapon is delivered to targets, often represented as crawling Internet websites such as conference deliverable Installation of a remote access trojan or backdoor on the victim system allows the adversary to maintain persistence inside the environment. payload, typically by means of an automated tool Transmission of the weapon to the exploitation triggers intruders code. Most often, exploitation targets an application or operating system vulnerability compromised hosts must beacon outbound to an Internet controller server to establish a C2 channel (weaponizer) environment using vectors like email attachments, Typically this objective is data exfiltration which involves collecting, encrypting and extracting information from proceedings andIncreasingly, client mailing lists forpplications data email addresses, files such as Adobe PDF or Microsoft websites, and USB removable media. social relationships, or information on specific technologies Office documents serve as the weaponized deliverable im environment Detect, DisruptDegrade Deceive Destroy Leverage, discover, analyze Atomic, computed and behavior indicators Campaign Analysis - Tools, Techniques and Procedures Intrusion Kill Chain Actions on Reconnaissance Weaponization Delivery Exploitation Installation Control (C2) Research, Only now, after progressing through the first six phases, can intruders take actions to achieve their original identificationCoupling a remote an exploit into a After the weapon is delivered to targets, often represented as crawling Internet websites such as conference deliverable Installation of a remote access trojan or backdoor on the victim system allows the adversary to maintain persistence inside the environment. payload, typically by means of an automated tool Transmission of the weapon to the exploitation triggers intruders code. Most often, exploitation targets an application or operating system vulnerability compromised hosts must beacon outbound to an Internet controller server to establish a C2 channel (weaponizer) environment using vectors like email attachments, Typically this objective is data exfiltration which involves collecting, encrypting and extracting information from proceedings andIncreasingly, client mailing lists forpplications data email addresses, files such as Adobe PDF or Microsoft websites, and USB removable media. social relationships, or information on specific technologies Office documents serve as the weaponized deliverable im environment Detect, DisruptDegrade Deceive Destroy Leverage, discover, analyze Atomic, computed and behavior indicators Campaign Analysis - Tools, Techniques and Procedures