Answered step by step
Verified Expert Solution
Question
1 Approved Answer
must be written in assembly code Design the program to decompress the data sequence saved in the .data section (COMPRESSED) and store the decompressed data
must be written in assembly code
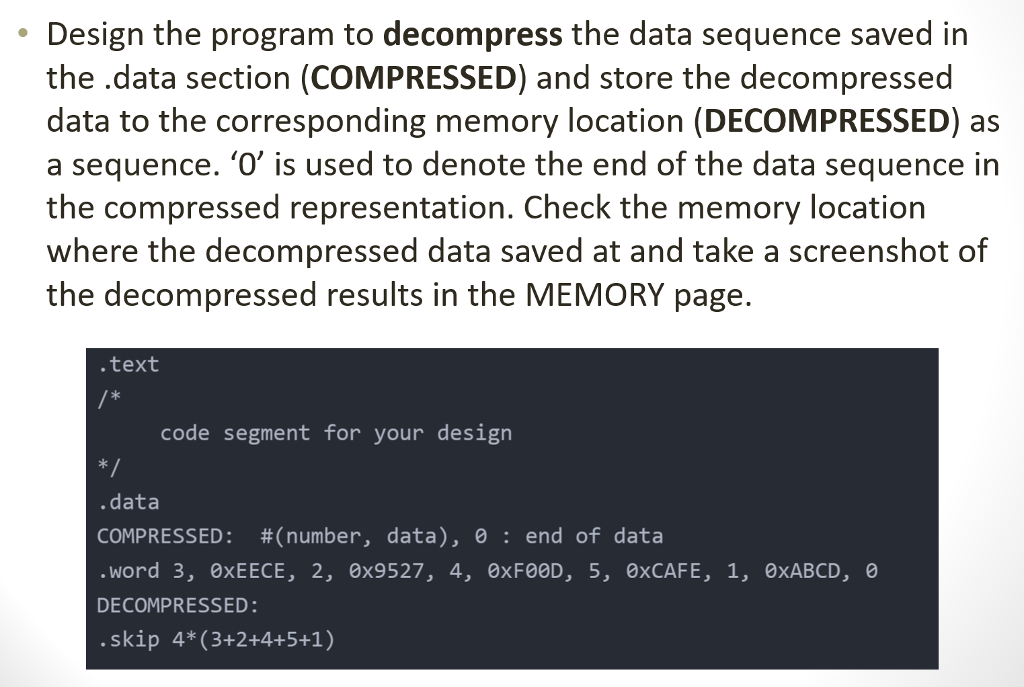
Design the program to decompress the data sequence saved in the .data section (COMPRESSED) and store the decompressed data to the corresponding memory location (DECOMPRESSED) as a sequence. '0' is used to denote the end of the data sequence in the compressed representation. Check the memory location where the decompressed data saved at and take a screenshot of the decompressed results in the MEMORY page. .text code segment for your design .data COMPRESSED: #(number, data), 0 : end of data word 3, 0xEECE, 2, 0x9527, 4, 0xF00D, 5, 0xCAFE, 1, 0xABCD, 0 DECOMPRESSED .skip 4* (3+2+4+5+1) Design the program to decompress the data sequence saved in the .data section (COMPRESSED) and store the decompressed data to the corresponding memory location (DECOMPRESSED) as a sequence. '0' is used to denote the end of the data sequence in the compressed representation. Check the memory location where the decompressed data saved at and take a screenshot of the decompressed results in the MEMORY page. .text code segment for your design .data COMPRESSED: #(number, data), 0 : end of data word 3, 0xEECE, 2, 0x9527, 4, 0xF00D, 5, 0xCAFE, 1, 0xABCD, 0 DECOMPRESSED .skip 4* (3+2+4+5+1)
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


