Answered step by step
Verified Expert Solution
Question
1 Approved Answer
need help with lab what was noticed during the tasks or steps. couple hours left Hands-On Projects Note If you are concerned about installing any
need help with lab what was noticed during the tasks or steps. couple hours left
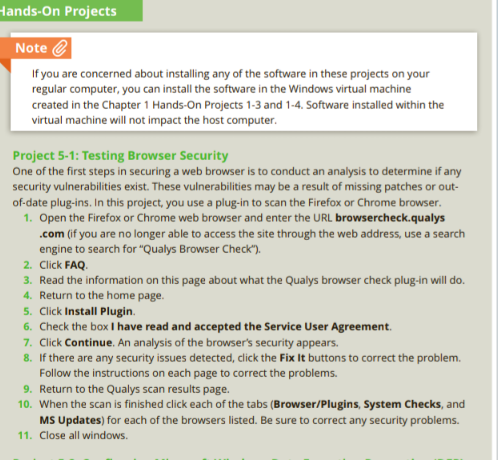
Hands-On Projects Note If you are concerned about installing any of the software in these projects on your regular computer, you can install the software in the Windows virtual machine created in the Chapter 1 Hands-On Projects 1-3 and 1-4. Software installed within the virtual machine will not impact the host computer. Project 5-1: Testing Browser Security One of the first steps in securing a web browser is to conduct an analysis to determine if any security vulnerabilities exist. These vulnerabilities may be a result of missing patches or out- of-date plug-ins. In this project, you use a plug-in to scan the Firefox or Chrome browser. 1. Open the Firefox or Chrome web browser and enter the URL browsercheck.qualys .com (if you are no longer able to access the site through the web address, use a search engine to search for "Qualys Browser Check"). 2. Click FAQ 3. Read the information on this page about what the Qualys browser check plug-in will do. 4. Return to the home page 5. Click Install Plugin 6. Check the box I have read and accepted the Service User Agreement. 7. Click Continue. An analysis of the browser's security appears. 8. If there are any security issues detected, click the Fix It buttons to correct the problem. Follow the instructions on each page to correct the problems. 9. Return to the Qualys scan results page. 10. When the scan is finished click each of the tabs (Browser/Plugins, System Checks, and MS Updates) for each of the browsers listed. Be sure to correct any security problems. 11. Close all windows Observation (what did you do, see, notice?) Write a short paragraph. You may add a couple of screen-shots. . . Answer the lab questions Answer any HOP step that has a question in it (i.e. has "?") Indicate the step # for each answer . Conclusion (what did you learn from completing this?) Write a short paragraph. Hands-On Projects Note If you are concerned about installing any of the software in these projects on your regular computer, you can install the software in the Windows virtual machine created in the Chapter 1 Hands-On Projects 1-3 and 1-4. Software installed within the virtual machine will not impact the host computer. Project 5-1: Testing Browser Security One of the first steps in securing a web browser is to conduct an analysis to determine if any security vulnerabilities exist. These vulnerabilities may be a result of missing patches or out- of-date plug-ins. In this project, you use a plug-in to scan the Firefox or Chrome browser. 1. Open the Firefox or Chrome web browser and enter the URL browsercheck.qualys .com (if you are no longer able to access the site through the web address, use a search engine to search for "Qualys Browser Check"). 2. Click FAQ 3. Read the information on this page about what the Qualys browser check plug-in will do. 4. Return to the home page 5. Click Install Plugin 6. Check the box I have read and accepted the Service User Agreement. 7. Click Continue. An analysis of the browser's security appears. 8. If there are any security issues detected, click the Fix It buttons to correct the problem. Follow the instructions on each page to correct the problems. 9. Return to the Qualys scan results page. 10. When the scan is finished click each of the tabs (Browser/Plugins, System Checks, and MS Updates) for each of the browsers listed. Be sure to correct any security problems. 11. Close all windows Observation (what did you do, see, notice?) Write a short paragraph. You may add a couple of screen-shots. . . Answer the lab questions Answer any HOP step that has a question in it (i.e. has "?") Indicate the step # for each answer . Conclusion (what did you learn from completing this?) Write a short paragraphStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started