Answered step by step
Verified Expert Solution
Question
1 Approved Answer
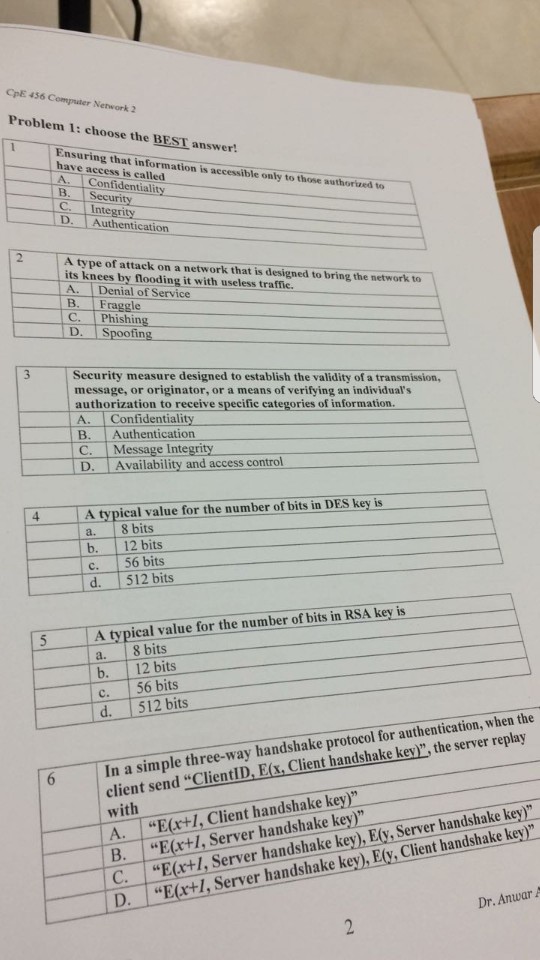
net work q Ensuring that information is accessible only to those authorized to have access is called A. Confidentiality B. Security C. Integrity D. Authentication
net work q
Ensuring that information is accessible only to those authorized to have access is called A. Confidentiality B. Security C. Integrity D. Authentication A type of attack on a network that is designed to bring the network to its knees by flooding it with useless traffic. A. Denial of Service B. Fraggle C, Phishing D. Spoofing Security measure desinged to establish the validity of a transmission, message, or originator, or a means of verifying an individual's authorization to receive specific categories of information. A. Confidentiality B. Authentication C. Message Integrity D. Availability and access control A typical value for the number of bits in RSA key is a. 8 bits b. 12 bits c. 56 bits d. 512 bits In a simple three-way handshake protocol tor authentication, when the client send "ClientID, E(x, Client handshake key)", the server replay with A. uE(x +I, Client handshake key)" B. "E(x + I, Server handshake key)" C. "E(x + I, Server handshake key), E(y, Server handshake key)" D. "E(x + I, Server handshake key), E(y, Client handshake key)Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started