Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Note: In this part of the lab, you will review an access control system against the PCI DSS risk assessment framework. Your task is to
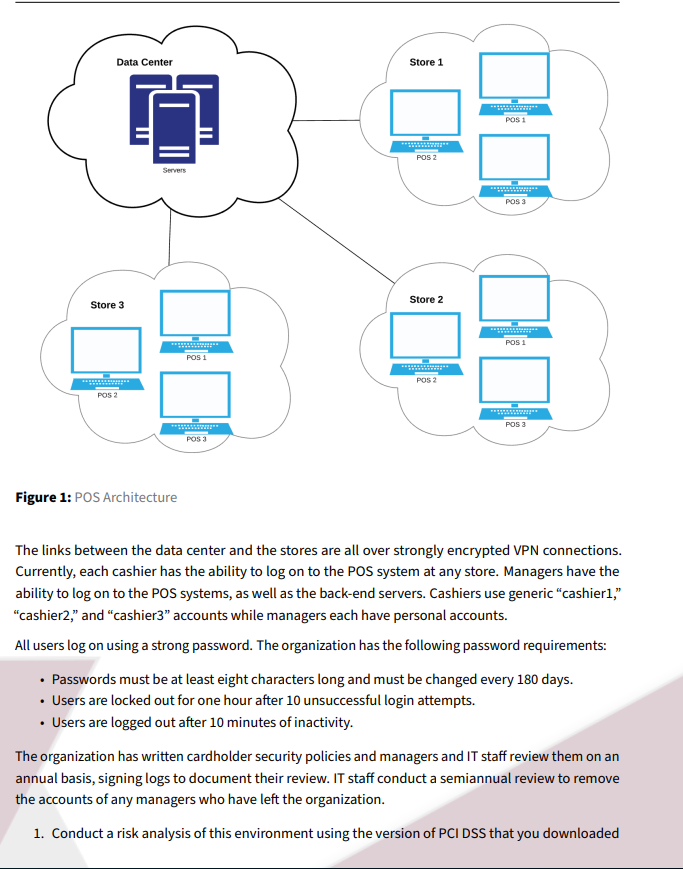
Note: In this part of the lab, you will review an access control system against the PCI DSS risk assessment framework. Your task is to identify any gaps that might exist between the existing system and the requirements in the standard. You are the security administrator for Ricky's Fried Chicken, a franchised fried chicken restaurant. The restaurant accepts credit cards and, as such, is subject to the provisions of PCI DSS. You are conducting a risk assessment of the point-of-sale (POS) system used by the chain against the access control provisions of PCl DSS. The POS uses the architecture shown below: Figure 1: POS Architecture The links between the data center and the stores are all over strongly encrypted VPN connections. Currently, each cashier has the ability to log on to the POS system at any store. Managers have the ability to log on to the POS systems, as well as the back-end servers. Cashiers use generic "cashier1," "cashier2," and "cashier3" accounts while managers each have personal accounts. All users log on using a strong password. The organization has the following password requirements: - Passwords must be at least eight characters long and must be changed every 180 days. - Users are locked out for one hour after 10 unsuccessful login attempts. - Users are logged out after 10 minutes of inactivity. The organization has written cardholder security policies and managers and IT staff review them on an annual basis, signing logs to document their review. IT staff conduct a semiannual review to remove the accounts of any managers who have left the organization. 1. Conduct a risk analysis of this environment using the version of PCI DSS that you downloaded in Part 1 of this lab. Document at least five control gaps that exist in the environment. You may make assumptions about information not provided in this scenario, if necessary. 2. Identify controls that will mitigate each of the five deficiencies you identified in the previous step. Create a prioritized list of these actions
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


