Answered step by step
Verified Expert Solution
Question
1 Approved Answer
number 15. operating system. 14. Fill in the blank. (Your answer must be all lower-case letters with correct spelling. Do not enter any punctuation mark.)
number 15. operating system.
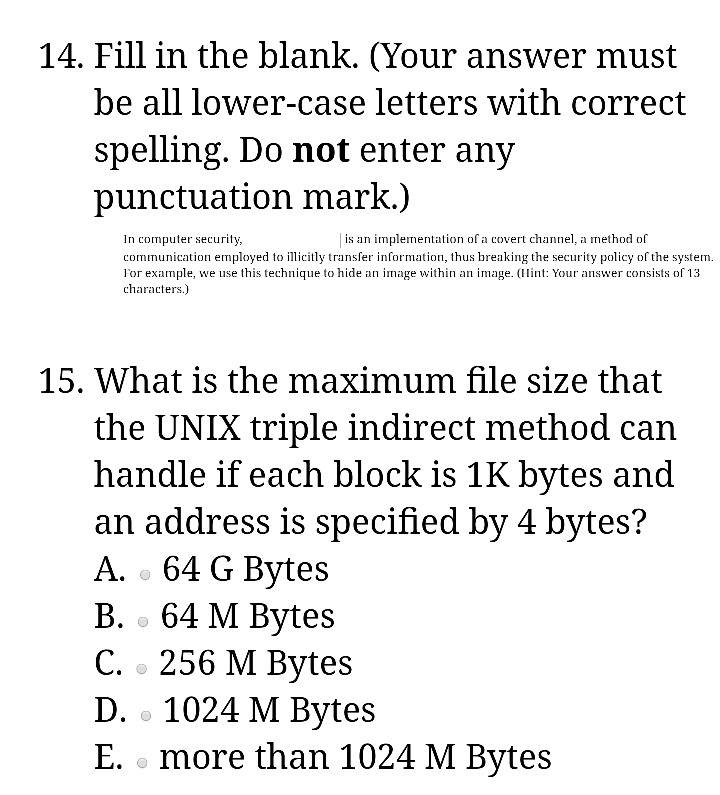
14. Fill in the blank. (Your answer must be all lower-case letters with correct spelling. Do not enter any punctuation mark.) In computer securitv communication employed to illicitly transfer information, thus breaking the security policy of the system l'or example, we use this technique to hide an image within an image. (n: Youranswer consists of 13 characters.) is an impleton of a covert channel, a method of 15, What is the maximum file size that the UNIX triple indirect method can handle if each block is 1K bytes and an address is specified by 4 bytes? A. -64 G Bytes B. 64 M Bytes C. 256 M Bytes D. o 1024 M Bytes E. more than 1024 M BytesStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


