Answered step by step
Verified Expert Solution
Question
1 Approved Answer
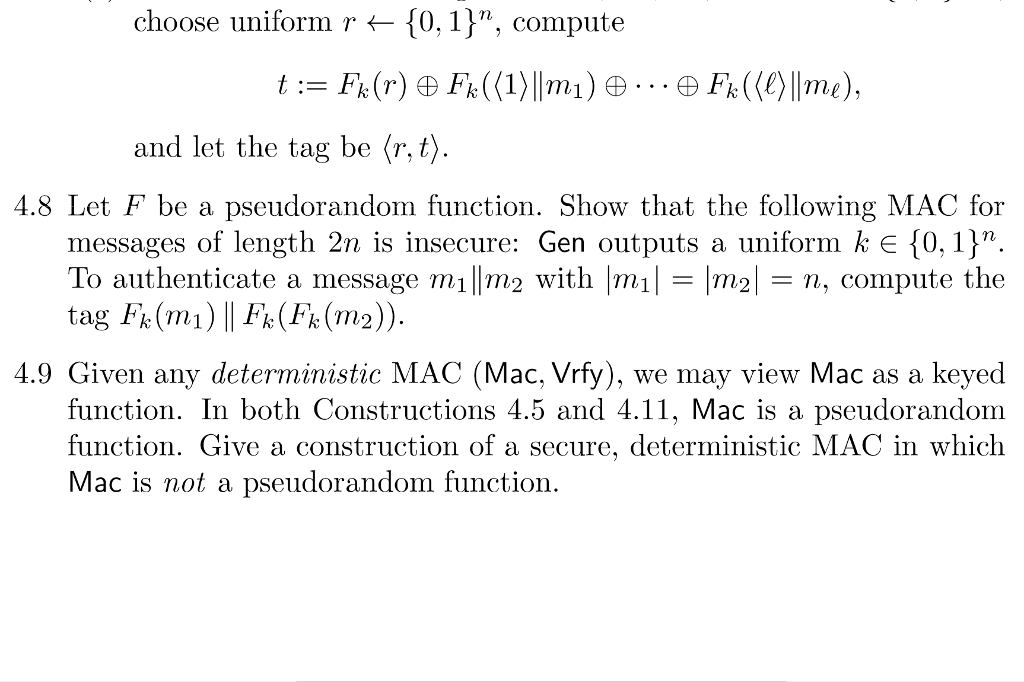
Only 4.8 choose uniform r {01 1}n, compute and let the tag be r, t 4.8 Let F be a pseudorandom function. Show that the
Only 4.8
choose uniform r {01 1}n, compute and let the tag be r, t 4.8 Let F be a pseudorandom function. Show that the following MAC for messages of length 2n is insecure: Gen outputs a uniform k e 10,11n To authenticate a message milm2 with |mmn, compute the 4.9 Given any deterministic MAC (Mac, Vrfy), we may view Mac as a keyed function. In both Constructions 4.5 and 4.11, Mac is a pseudorandom function. Give a construction of a secure, deterministic MAC in which Mac is not a pseudorandom function choose uniform r {01 1}n, compute and let the tag be r, t 4.8 Let F be a pseudorandom function. Show that the following MAC for messages of length 2n is insecure: Gen outputs a uniform k e 10,11n To authenticate a message milm2 with |mmn, compute the 4.9 Given any deterministic MAC (Mac, Vrfy), we may view Mac as a keyed function. In both Constructions 4.5 and 4.11, Mac is a pseudorandom function. Give a construction of a secure, deterministic MAC in which Mac is not a pseudorandom functionStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started