Answered step by step
Verified Expert Solution
Question
1 Approved Answer
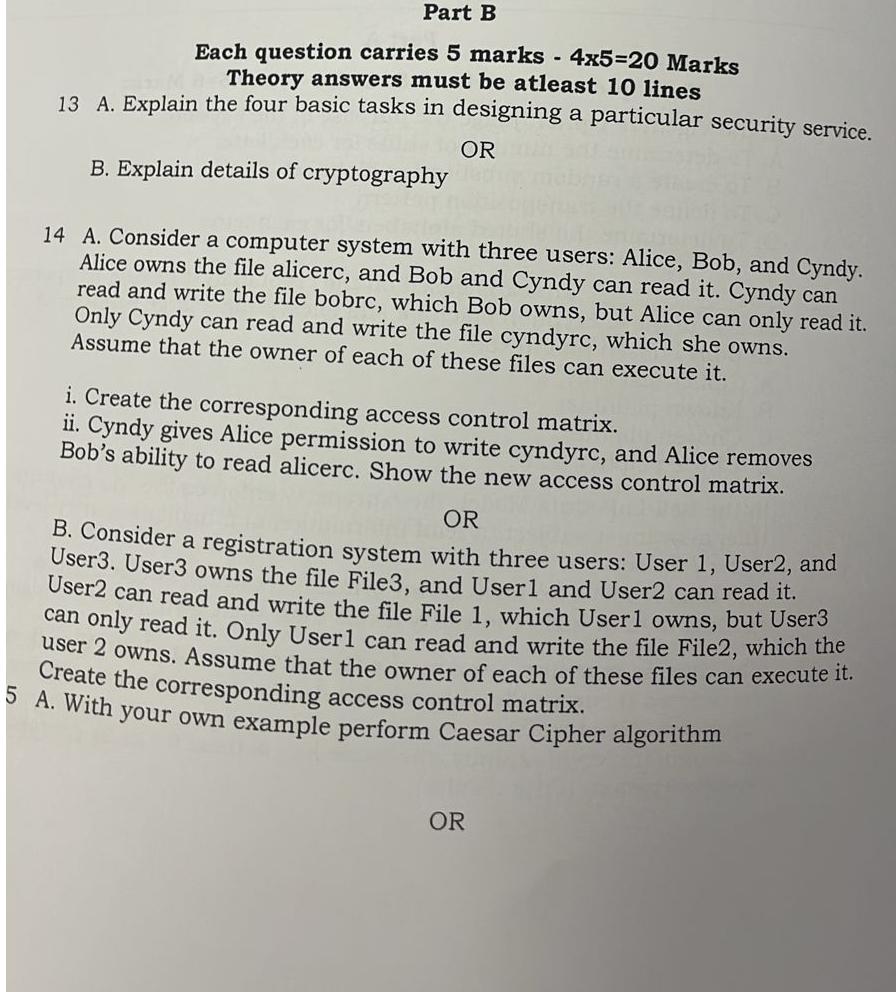
Part B Each question carries 5 marks - 4 x 5 = 2 0 Marks Theory answers must be atleast 1 0 lines 1 3
Part B
Each question carries marks x Marks
Theory answers must be atleast lines
A Explain the four basic tasks in designing a particular security service.
OR
B Explain details of cryptography
A Consider a computer system with three users: Alice, Bob, and Cyndy Alice owns the file alicerc, and Bob and Cyndy can read it Cyndy can read and write the file bobrc, which Bob owns, but Alice can only read it Only Cyndy can read and write the file cyndyrc which she owns. Assume that the owner of each of these files can execute it
i Create the corresponding access control matrix.
ii Cyndy gives Alice permission to write cyndyrc and Alice removes Bob's ability to read alicerc. Show the new access control matrix.
OR
B Consider a registration system with three users: User User and User User owns the file File and User and User can read it User can read and write the file File which User owns, but User can only read it Only User can read and write the file File which the user owns. Assume that the owner of each of these files can execute it Create the corresponding access control matrix.
A With your own example perform Caesar Cipher algorithm
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started