Question
Part III 802.11 Review the first capture file (Nokia) and determine what is happening with the 802.11 traffic. Hint: use the Analyze/Conversation Filter Describe the
Part III 802.11
Review the first capture file (Nokia) and determine what is happening with the 802.11 traffic. Hint: use the Analyze/Conversation Filter
Describe the traffic: what packets are involved and what is happening? (include source, destination, time of capture)
Take a screenshot of the actual packets within the capture file that you observed this behavior.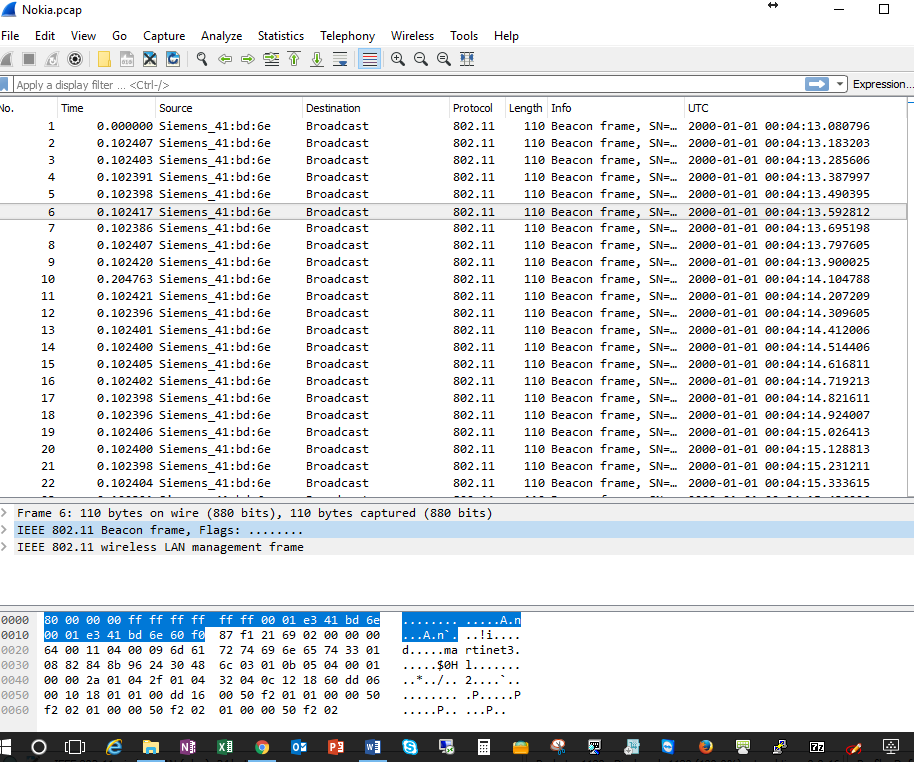
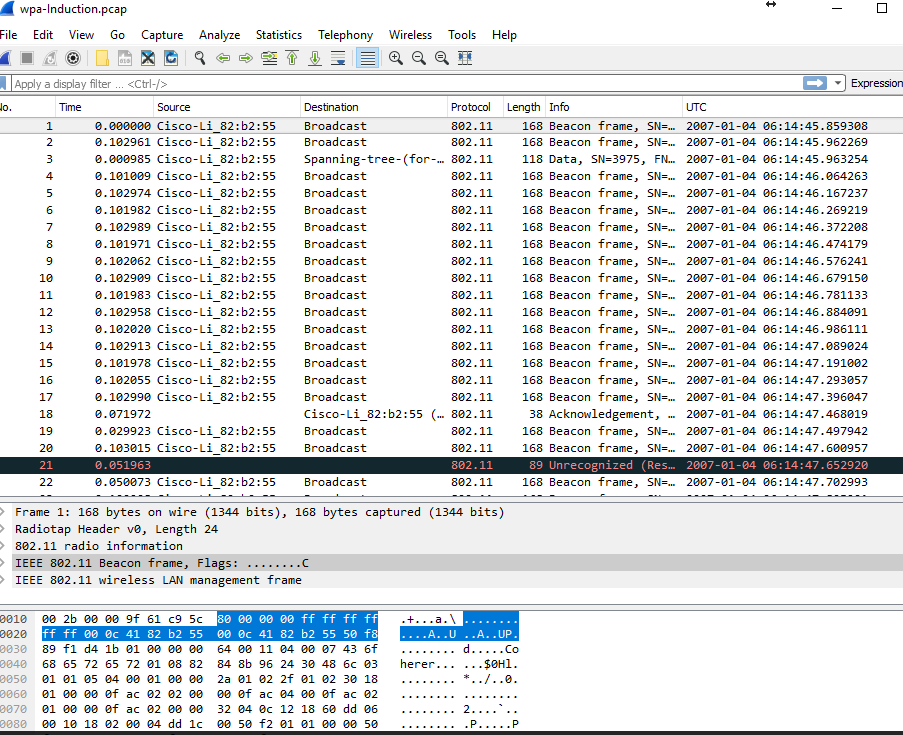
Review the second capture file (wpa) and determine what is happening with the WPA traffic in this capture. (password is Induction). Hint: Use Edit->preferences, Protocol IEEE 802.11, decryption with Induction); Look at the packets prior to and after decryption. Use this
https://wiki.wireshark.org/HowToDecrypt802.11 . You are STILL required to answer the following questions in your own words and provide a screenshot!
What do you different once you have decrypted the packets? What is decrypted and what is happening? (include source, destination, time of capture)
Take a screenshot of the actual packets within the capture file that you observed.
Part IV Ipv6 Ipv4
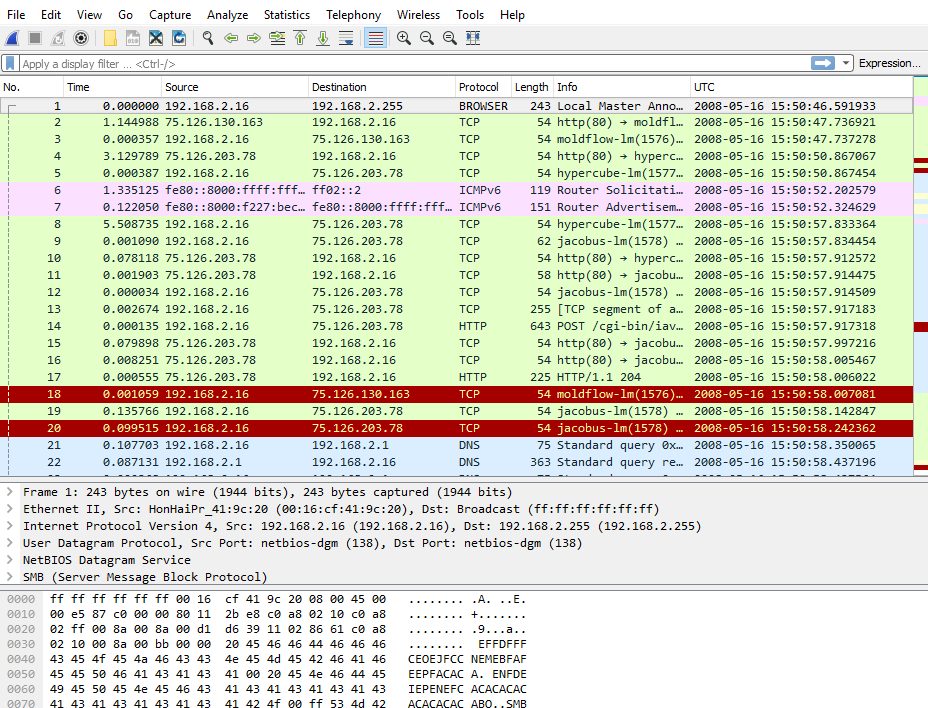
Review the third capture file (toredo) and determine what is happening with the Ipv4-IPv6 traffic in this capture.
a. Research Toredo for encapsulation relating to Ipv6 using the content links in the course and describe it here.
Describe the traffic: what packets are involved and what is happening? (include source, destination, time of capture) (Hint: look at all Ipv6 packets that have Toredo in their details)
Take a screenshot of the actual packets within the capture file that you observed this behavior.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


