Pease answer ALL questions carefully
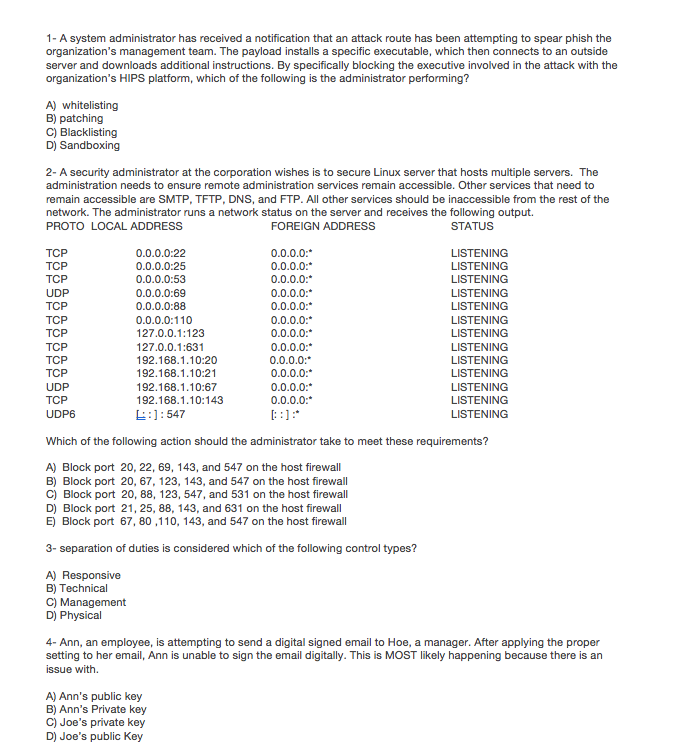
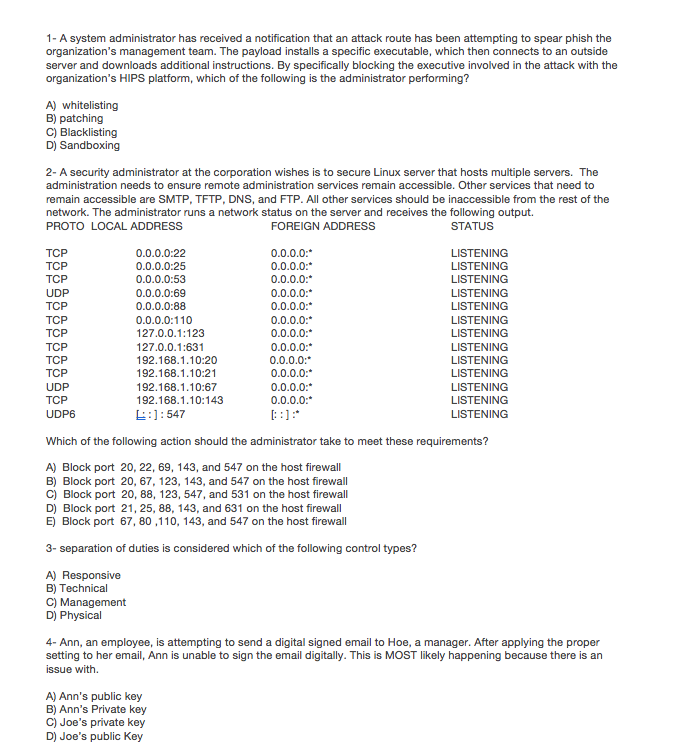
1- A system administrator has received a notification that an attack route has been attempting to spear phish the organization's management team. The payload installs a specific executable, which then connects to an outside server and downloads additional instructions. By specifically blocking the executive involved in the attack with the organization's HIPS platform, which of the following is the administrator performing? A) whitelisting B) patching C) Blacklisting 2- A security administrator at the corporation wishes is to secure Linux server that hosts multiple servers. The administration needs to ensure remote administration services remain accessible. Other services that need to remain accessible are SMTP, TFTP, DNS, and FTP. All other services should be inaccessible from the rest of the network. The administrator runs a network status on the server and receives the following output. PROTO LOCAL ADDRESS FOREIGN ADDRESS STATUS TCP TCP TCP UDP TCP TCP TCP TCP TCP TCP UDP TCP UDP6 0.0.0.0:22 0.0.0.0:25 0.0.0.0:53 0.0.0.0:69 0.0.0.0:88 0.0.0.0:110 127.0.0.1:123 127.0.0.1:631 192.168.1.10:20 192.168.1.10:21 192.168.1.10:67 192.168.1.10:143 L:]:547 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING Which of the following action should the administrator take to meet these requirements? A) Block port 20, 22, 69, 143, and 547 on the host firewall B) Block port 20, 67, 123, 143, and 547 on the host firewall C) Block port 20, 88, 123, 547, and 531 on the host firewall D) Block port 21, 25, 88, 143, and 631 on the host firewall E) Block port 67, 80,110, 143, and 547 on the host firewall 3- separation of duties is considered which of the following control types? B) Technical C) Management D) Physical 4- Ann, an employee, is attempting to send a digital signed email to Hoe, a manager. After applying the proper setting to her email, Ann is unable to sign the email digitally. This is MOST likely happening because there is an issue with. A) Ann's public key B) Ann's Private key C) Joe's private key D) Joe's public Key 1- A system administrator has received a notification that an attack route has been attempting to spear phish the organization's management team. The payload installs a specific executable, which then connects to an outside server and downloads additional instructions. By specifically blocking the executive involved in the attack with the organization's HIPS platform, which of the following is the administrator performing? A) whitelisting B) patching C) Blacklisting 2- A security administrator at the corporation wishes is to secure Linux server that hosts multiple servers. The administration needs to ensure remote administration services remain accessible. Other services that need to remain accessible are SMTP, TFTP, DNS, and FTP. All other services should be inaccessible from the rest of the network. The administrator runs a network status on the server and receives the following output. PROTO LOCAL ADDRESS FOREIGN ADDRESS STATUS TCP TCP TCP UDP TCP TCP TCP TCP TCP TCP UDP TCP UDP6 0.0.0.0:22 0.0.0.0:25 0.0.0.0:53 0.0.0.0:69 0.0.0.0:88 0.0.0.0:110 127.0.0.1:123 127.0.0.1:631 192.168.1.10:20 192.168.1.10:21 192.168.1.10:67 192.168.1.10:143 L:]:547 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: 0.0.0.0: LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING Which of the following action should the administrator take to meet these requirements? A) Block port 20, 22, 69, 143, and 547 on the host firewall B) Block port 20, 67, 123, 143, and 547 on the host firewall C) Block port 20, 88, 123, 547, and 531 on the host firewall D) Block port 21, 25, 88, 143, and 631 on the host firewall E) Block port 67, 80,110, 143, and 547 on the host firewall 3- separation of duties is considered which of the following control types? B) Technical C) Management D) Physical 4- Ann, an employee, is attempting to send a digital signed email to Hoe, a manager. After applying the proper setting to her email, Ann is unable to sign the email digitally. This is MOST likely happening because there is an issue with. A) Ann's public key B) Ann's Private key C) Joe's private key D) Joe's public Key