Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Please code in MATLAB in possible. I am very curious how this works but my coding knowledge is not sufficient enough to perform it Problem
Please code in MATLAB in possible. I am very curious how this works but my coding knowledge is not sufficient enough to perform it
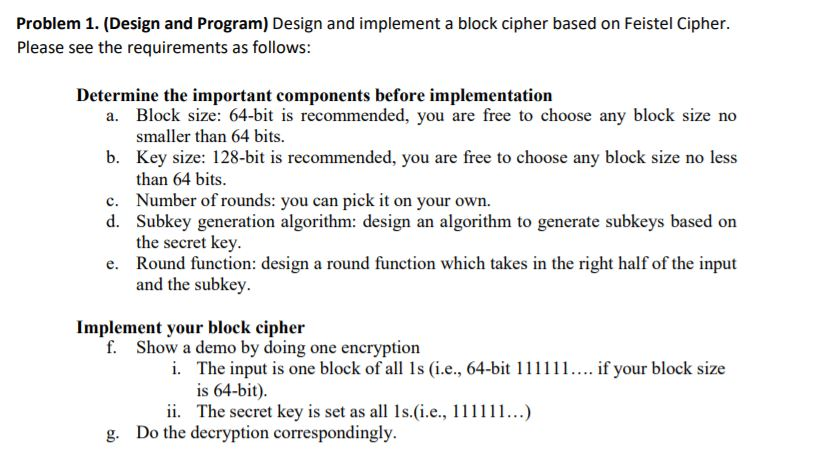
Problem 1. (Design and Program) Design and implement a block cipher based on Feistel Cipher. Please see the requirements as follows: Determine the important components before implementation a. Block size: 64-bit is recommended, you are free to choose any block size no smaller than 64 bits. b. Key size: 128-bit is recommended, you are free to choose any block size no less than 64 bits. c. Number of rounds: you can pick it on your own. d. Subkey generation algorithm: design an algorithm to generate subkeys based on the secret key. e. Round function: design a round function which takes in the right half of the input and the subkey. Implement your block cipher f. Show a demo by doing one encryption i. The input is one block of all is (i.e., 64-bit 111111.... if your block size is 64-bit). ii. The secret key is set as all 1s.(i.e., 111111...) g. Do the decryption correspondingly. Problem 1. (Design and Program) Design and implement a block cipher based on Feistel Cipher. Please see the requirements as follows: Determine the important components before implementation a. Block size: 64-bit is recommended, you are free to choose any block size no smaller than 64 bits. b. Key size: 128-bit is recommended, you are free to choose any block size no less than 64 bits. c. Number of rounds: you can pick it on your own. d. Subkey generation algorithm: design an algorithm to generate subkeys based on the secret key. e. Round function: design a round function which takes in the right half of the input and the subkey. Implement your block cipher f. Show a demo by doing one encryption i. The input is one block of all is (i.e., 64-bit 111111.... if your block size is 64-bit). ii. The secret key is set as all 1s.(i.e., 111111...) g. Do the decryption correspondinglyStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


