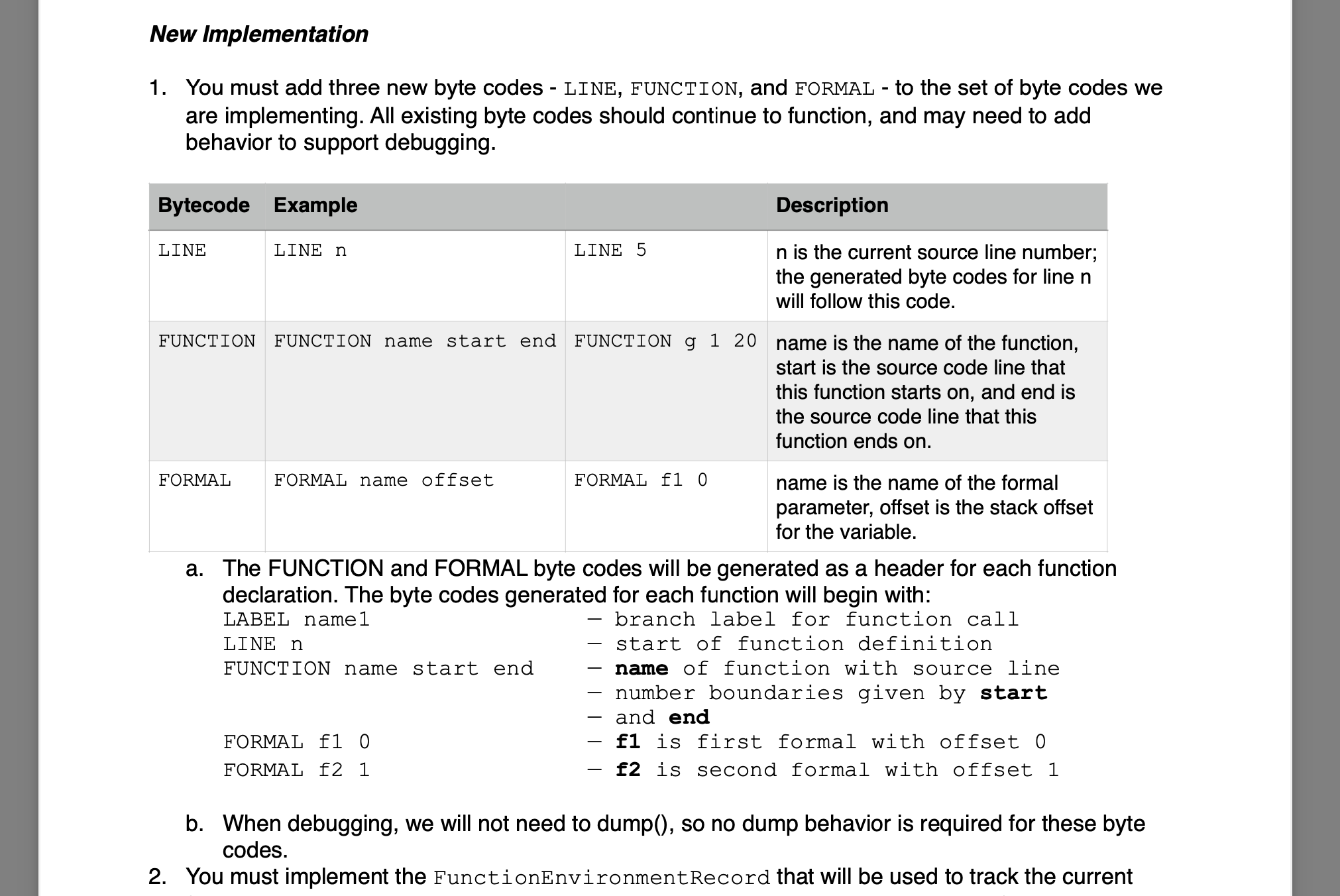
Please complete number 1 only. We need to add 3 byte code files as mentioned LINE, FUNCTION
Question:
Please complete number 1 only.
We need to add 3 byte code files as mentioned LINE, FUNCTION AND FORMAL.
One example of such code is CallCode.java provided below:
/*
* Transfer control to the indicated function
*/
package interpreter.ByteCode;
import interpreter.VirtualMachine;
import java.util.ArrayList;
public class CallCode extends BranchCode {
protected String functionName;
protected int targetAddress;
protected int value;
public void init(ArrayList args) {
functionName = args.get(0);
}
public void execute(VirtualMachine vm) {
vm.returnAddrs.push(vm.pc);
vm.pc = targetAddress;
value = vm.runStack.peek();
//verify if the dump is on
if("ON".equals(vm.dumpMode)) {
int n = functionName.indexOf("<");
String temp;
if(n<0){
temp = functionName;
}else{
temp = functionName.substring(0,n);
}
System.out.println("CALL " + functionName + " " + temp + "(" + value + ")");
}
}
public int getTargetAddress(){
return targetAddress;
}
public void setTargetAddress(int n){
targetAddress = n;
}
public String getLabel(){
return functionName;
}
}

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill




