Answered step by step
Verified Expert Solution
Question
1 Approved Answer
please give description too 2.6 Task 6: The PATH Environment Variable and Set-UID Programs Because of the shell program invoked, calling system () within a
please give description too
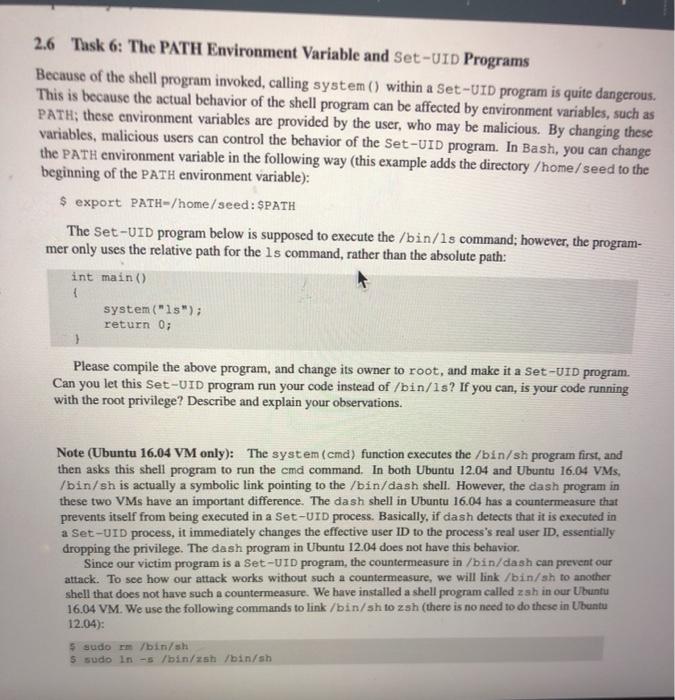
2.6 Task 6: The PATH Environment Variable and Set-UID Programs Because of the shell program invoked, calling system () within a Set-UID program is quite dangerous This is because the actual behavior of the shell program can be affected by environment variables, such as PATH; these environment variables are provided by the user, who may be malicious. By changing these variables, malicious users can control the behavior of the Set-UID program. In Bash, you can change the PATH environment variable in the following way (this example adds the directory /home/seed to the beginning of the PATH environment variable): $ export PATH-/home/seed: SPATH The Set-UID program below is supposed to execute the /bin/1s command; however, the program- mer only uses the relative path for the ls command, rather than the absolute path: int main() system("1s"); return 0; Please compile the above program, and change its owner to root, and make it a Set-UID program. Can you let this Set-UID program run your code instead of /bin/1s? If you can, is your code running with the root privilege? Describe and explain your observations. Note (Ubuntu 16.04 VM only): The system (cmd) function executes the /bin/sh program first, and then asks this shell program to run the cmd command. In both Ubuntu 12.04 and Ubuntu 16.04 VMs. /bin/sh is actually a symbolic link pointing to the /bin/dash shell. However, the dash program in these two VMs have an important difference. The dash shell in Ubuntu 16.04 has a countermeasure that prevents itself from being executed in a Set-UID process. Basically, if dash detects that it is executed in a Set-UID process, it immediately changes the effective user ID to the process's real user ID. essentially dropping the privilege. The dash program in Ubuntu 12.04 does not have this behavior. Since our victim program is a Set-UID program, the countermeasure in /bin/dash can prevent our attack. To see how our attack works without such a countermeasure, we will link /bin/sh to another shell that does not have such a countermeasure. We have installed a shell program called zah in our Ubuntu 16.04 VM. We use the following commands to link /bin/sh to zsh (there is no need to do these in Ubuntu 12.04): 5 sudom /bin/sh $ sudo in-s /bin/sh /bin/sh Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


