Answered step by step
Verified Expert Solution
Question
1 Approved Answer
please i want full clear solution DONOT COPY 15 points) User Authentication. (7 points) Consider the following proposed authentication protocol between Alice and Bob based
please i want full clear solution DONOT COPY 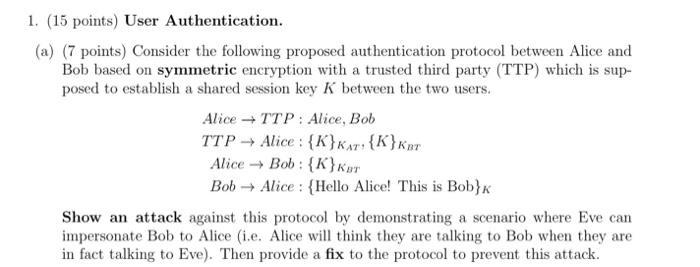
15 points) User Authentication. (7 points) Consider the following proposed authentication protocol between Alice and Bob based on symmetric encryption with a trusted third party (TTP) which is supposed to establish a shared session key K between the two users. AliceTTP:Alice,BobTTPAlice:{K}KAT,{K}KBTAliceBob:{K}KBTBobAlice:{HelloAlice!ThisisBob}K Show an attack against this protocol by demonstrating a scenario where Eve can impersonate Bob to Alice (i.e. Alice will think they are talking to Bob when they are in fact talking to Eve). Then provide a fix to the protocol to prevent this attack 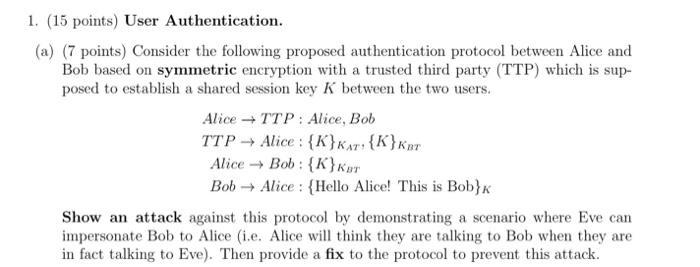
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started