Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Please provide correct solution according t o the question. Discuss in a three - to - five - page paper, the procedures, tools, and results
Please provide correct solution according the question. Discuss in a threetofivepage paper, the procedures, tools, and results for the first steps of the Chi Mak espionage investigation process model:
Identificationassessment
Preservation
Identification
Discuss: your preplanned strategy in preparing and approaching the crime scenes and if a valid search warrant was required; the physical and digital evidence from each of the crime scenes; determine the suspects and their activity; and describe the physical location of the crime scene and the possibility of cyberspace emails URLs equipment various types of wire and wireless hardware devices and software applications that you expect when approaching your digital crime scene. Preservation
Here, you will show the case management of your teams investigation. You will also show the chain of custody, and that the data you collected is not contaminated. Remember the physical and digital data that is acquired must be properly isolated, secured, and preserved.
In this digital investigation the original evidence data must never be touched. So here discuss if a forensically sound copy of your original data was made, and the examination and analysis of this data was performed on the forensic copy. For example, discuss if a storage device was mounted as readonly to assure the data was not modified or overwritten during the time the device was mounted.
In another example, state if copies of the digital data are acquired through a live acquisition process to capture digital evidence from memory of a running system.
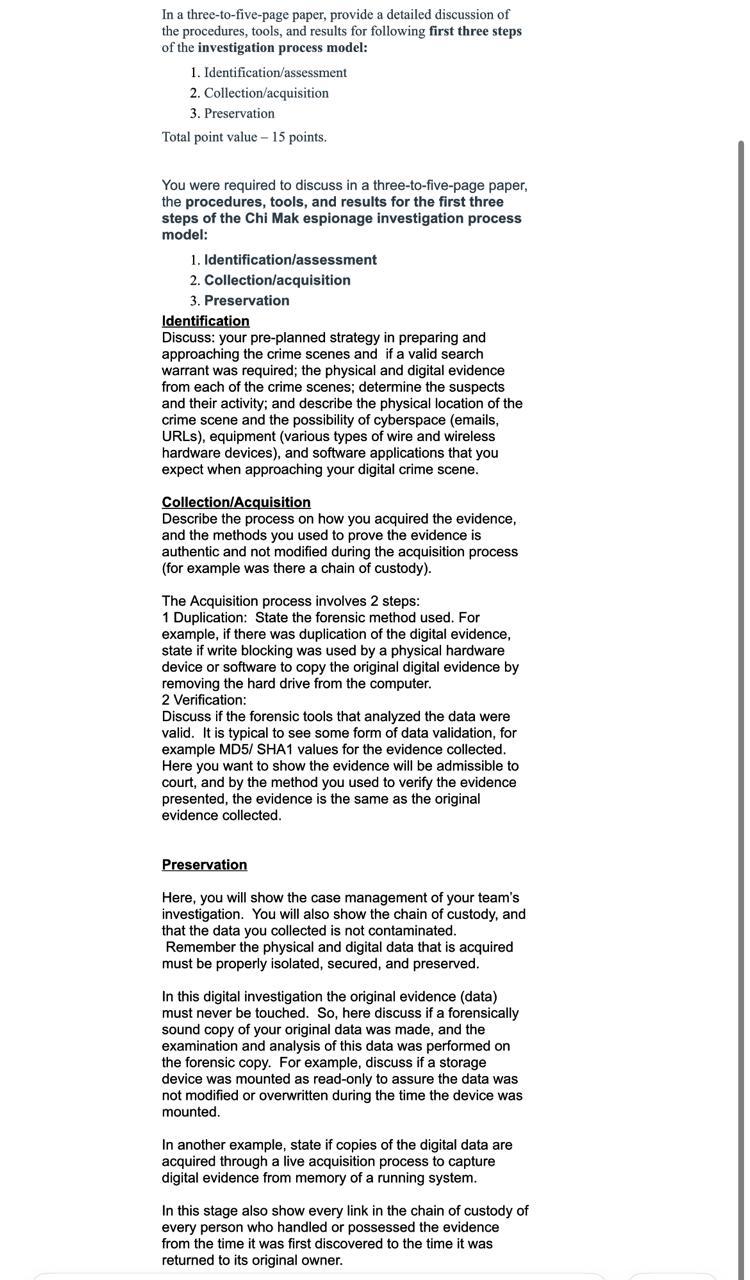
In this stage also show every link in the chain of custody of every person who handled or possessed the evidence from the time it was first discovered to the time it was returned to its original owner. In a threetofivepage paper, provide a detailed discussion of
the procedures, tools, and results for following first three steps
of the investigation process model:
Identificationassessment
Collectionacquisition
Preservation
Total point value points.
You were required to discuss in a threetofivepage paper,
the procedures, tools, and results for the first three
steps of the Chi Mak espionage investigation process
model:
Identificationassessment
Collectionacquisition
Preservation
Identification
Discuss: your preplanned strategy in preparing and
approaching the crime scenes and if a valid search
warrant was required; the physical and digital evidence
from each of the crime scenes; determine the suspects
and their activity; and describe the physical location of the
crime scene and the possibility of cyberspace emails
URLs equipment various types of wire and wireless
hardware devices and software applications that you
expect when approaching your digital crime scene.
CollectionAcquisition
Describe the process on how you acquired the evidence,
and the methods you used to prove the evidence is
authentic and not modified during the acquisition process
for example was there a chain of custody
The Acquisition process involves steps:
Duplication: State the forensic method used. For
example, if there was duplication of the digital evidence,
state if write blocking was used by a physical hardware
device or software to copy the original digital evidence by
removing the hard drive from the computer.
Verification:
Discuss if the forensic tools that analyzed the data were
valid. It is typical to see some form of data validation, for
example MD SHA values for the evidence collected.
Here you want to show the evidence will be admissible to
court, and by the method you used to verify the evidence
presented, the evidence is the same as the original
evidence collected.
Preservation
Here, you will show the case management of your team's
investigation. You will also show the chain of custody, and
that the data you collected is not contaminated.
Remember the physical and digital data that is acquired
must be properly isolated, secured, and preserved.
In this digital investigation the original evidence data
must never be touched. So here discuss if a forensically
sound copy of your original data was made, and the
examination and analysis of this data was performed on
the forensic copy. For example, discuss if a storage
device was mounted as readonly to assure the data was
not modified or overwritten during the time the device was
mounted.
In another example, state if copies of the digital data are
acquired through a live acquisition process to capture
digital evidence from memory of a running system.
In this stage also show every link in the chain of custody of
every person who handled or possessed the evidence
from the time it was first discovered to the time it was
returned to its original owner.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


