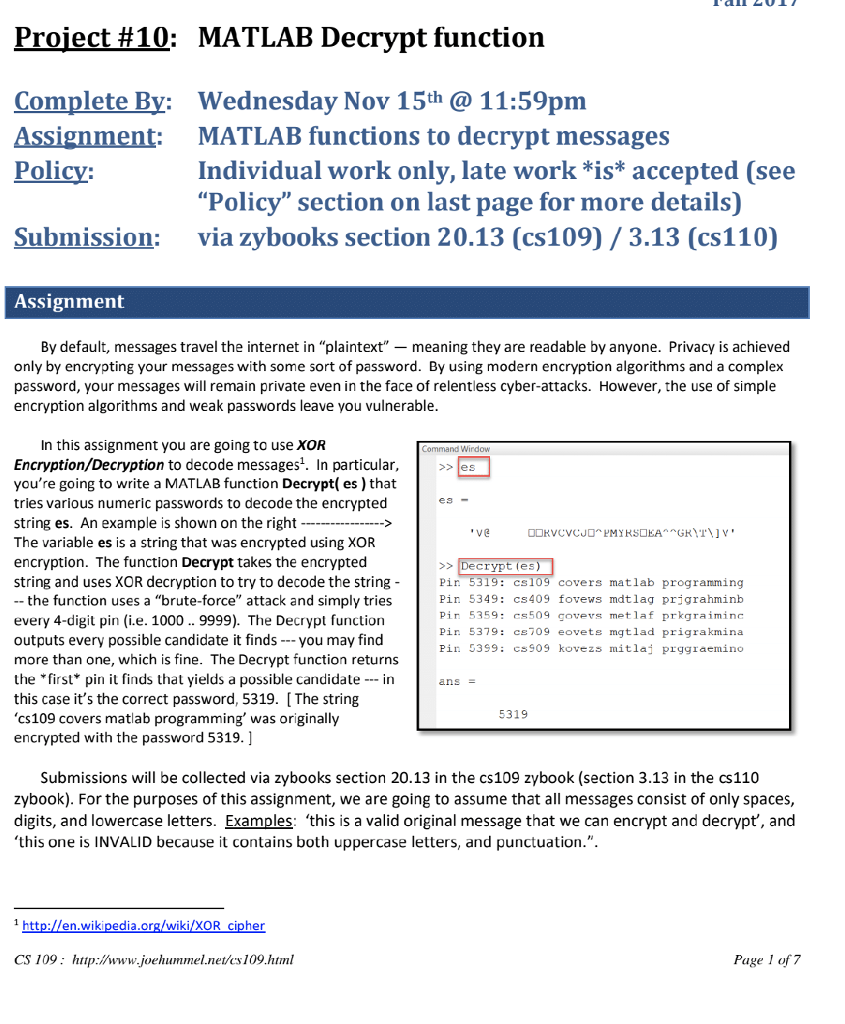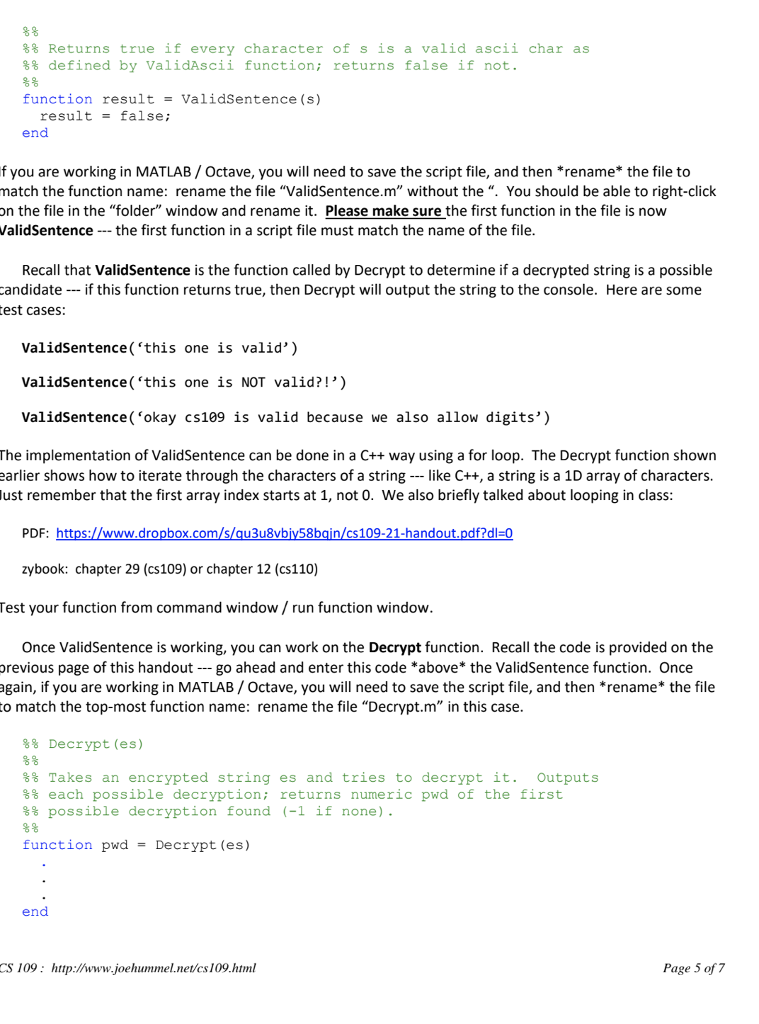
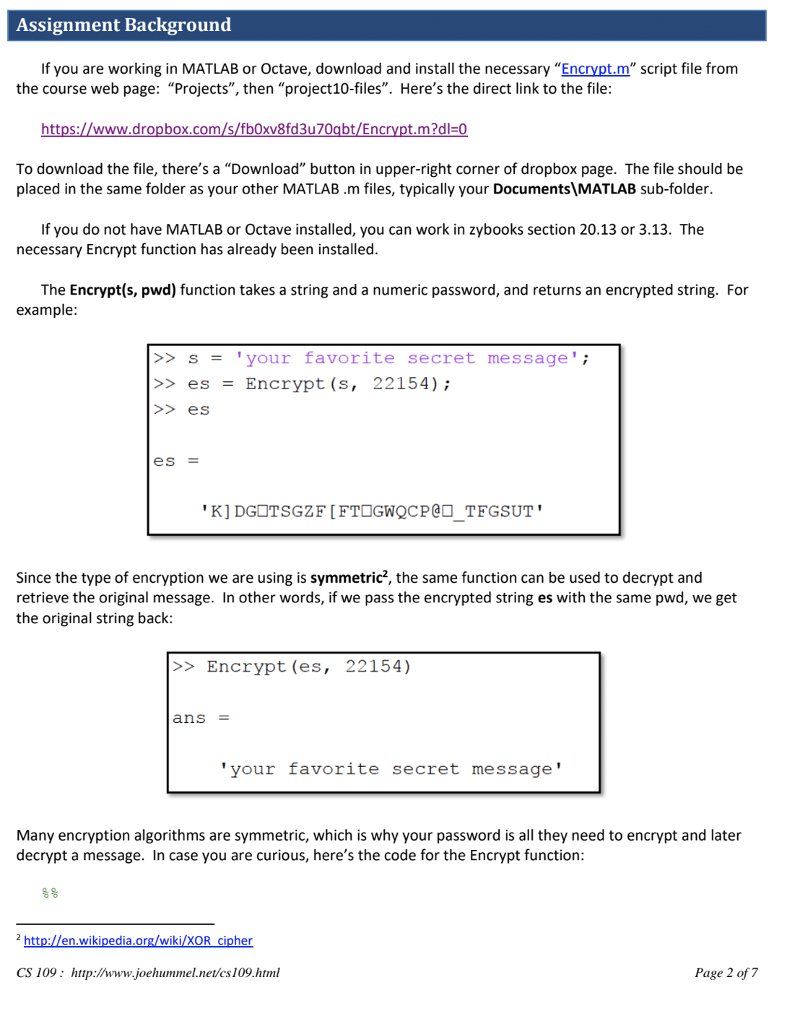
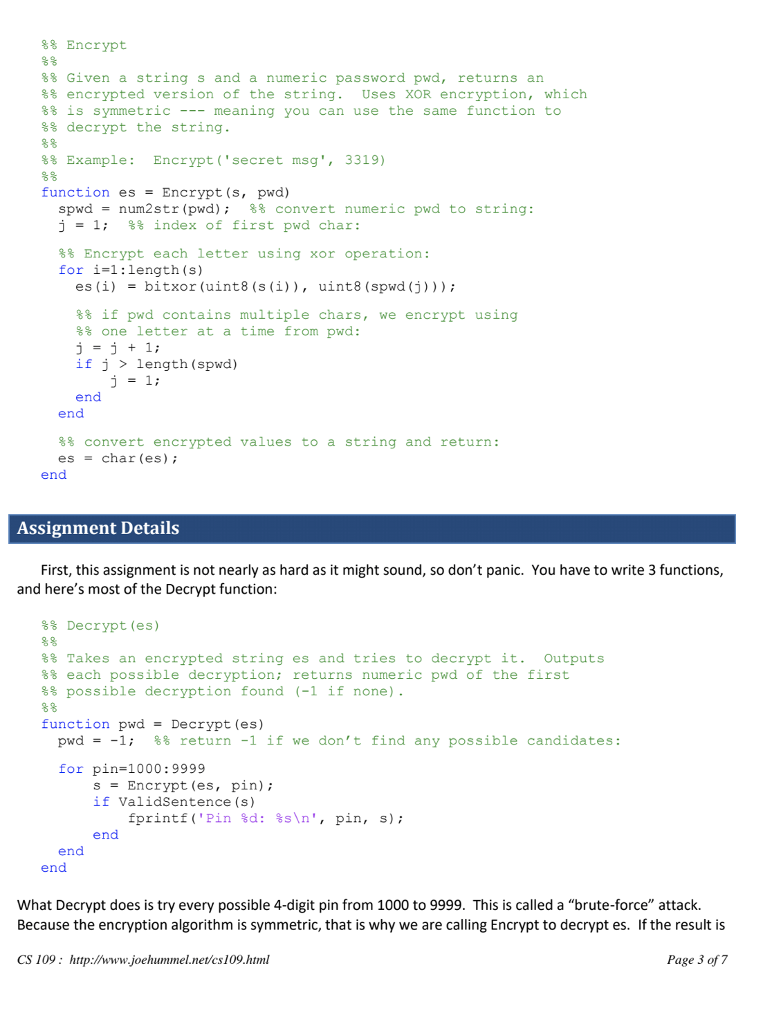
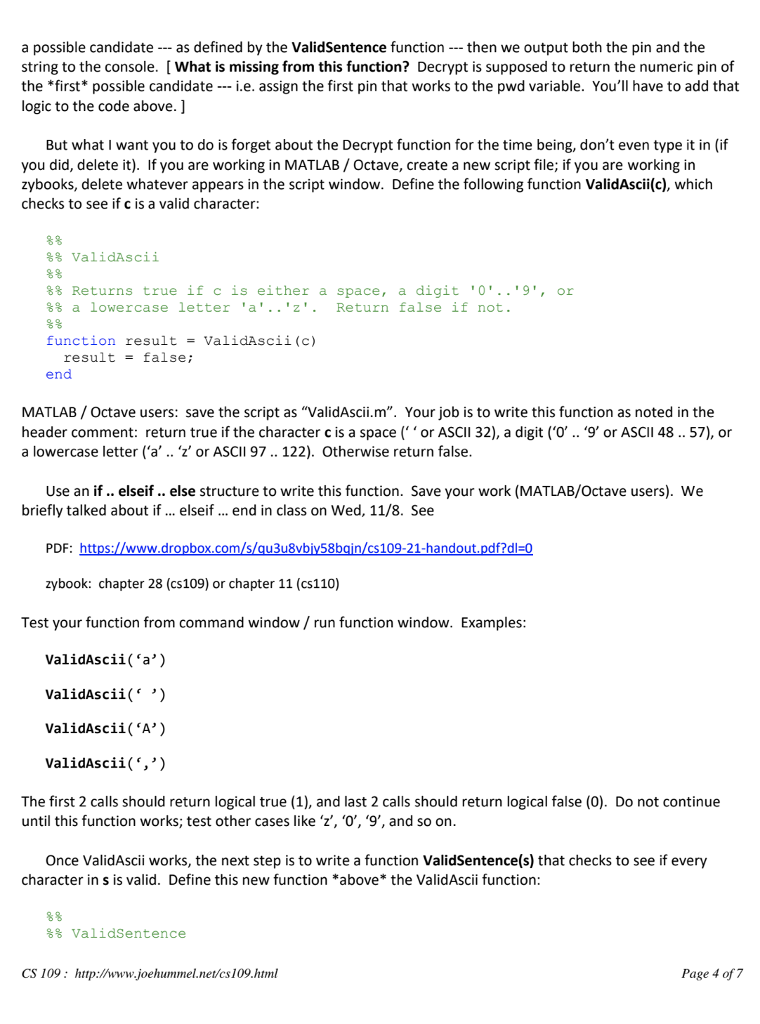
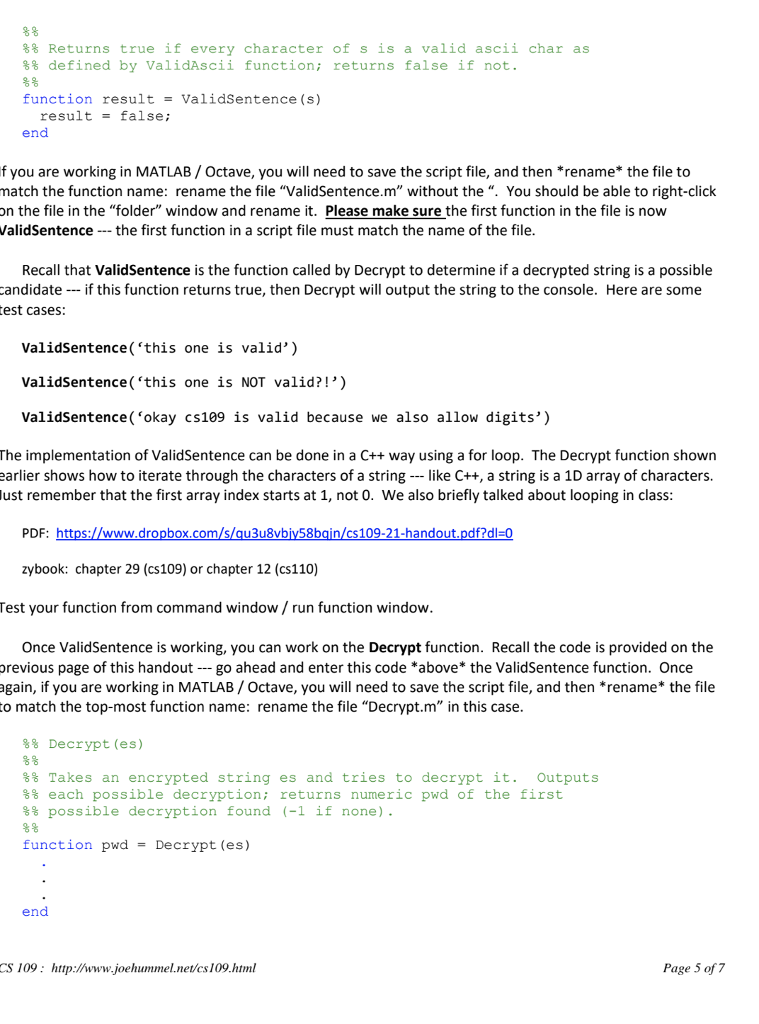
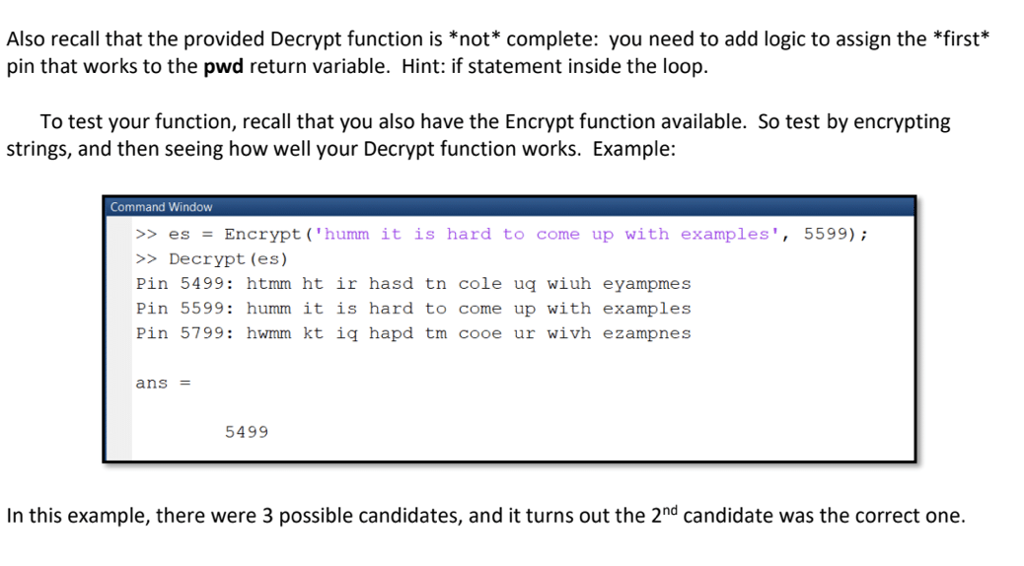
Project #10: MATLAB Decrypt function CompleteBy: Wednesday Nov 15th 11:59pm Assignment MATLAB functions to decrypt messages Policy Individual work only, late work *is* accepted (see "Policy" section on last page for more details) Submission: via zybooks section 20.13 (cs109) /3.13 (cs110) Assignment By default, messages travel the internet in "plaintext"-meaning they are readable by anyone. Privacy is achieved only by encrypting your messages with some sort of password. By using modern encryption algorithms and a complex password, your messages will remain private even in the face of relentless cyber-attacks. However, the use of simple encryption algorithms and weak passwords leave you vulnerable In this assignment you are going to use XOR Encryption/Decryption to decode messages1. In particular, you're going to write a MATLAB function Decrypt(es) that tries various numeric passwords to decode the encrypted string es. An example is shown on the right The variable es is a string that was encrypted using XOR encryption. The function Decrypt takes the encrypted string and uses XOR decryption to try to decode the string - - the function uses a "brute-force" attack and simply tries every 4-digit pin (i.e. 1000.. 9999). The Decrypt function outputs every possible candidate it finds you may find more than one, which is fine. The Decrypt function returns the first pin it finds that yields a possible candidate in this case it's the correct password, 5319. [The string 'CS109 covers matlab programming' was originally encrypted with the password 5319.] Wirdow > es es- >Decrypt (es Pir Pir 5349: cs409 fovews mdtlag prjgrahminb Pir 5359: cs509 govers metlaf prkgraiminc Pin 5379: cs709 eovets mgtlad prigrakmina Pir 53S9: cs909 kovezs mitlaj prggraemino covers matlab progranming ans E 5319 Submissions will be collected via zybooks section 20.13 in the cs109 zybook (section 3.13 in the cs110 zybook). For the purposes of this assignment, we are going to assume that all messages consist of only spaces, digits, and lowercase letters. Examples: 'this is a valid original message that we can encrypt and decrypt, and 'this one is INVALID because it contains both uppercase letters, and punctuation.". 1 http://en.wikipedia.org/wiki/XOR cipher CS 109: htup:lwww.joehummel.net/cs109.html Page I of'7