Q1/ ?
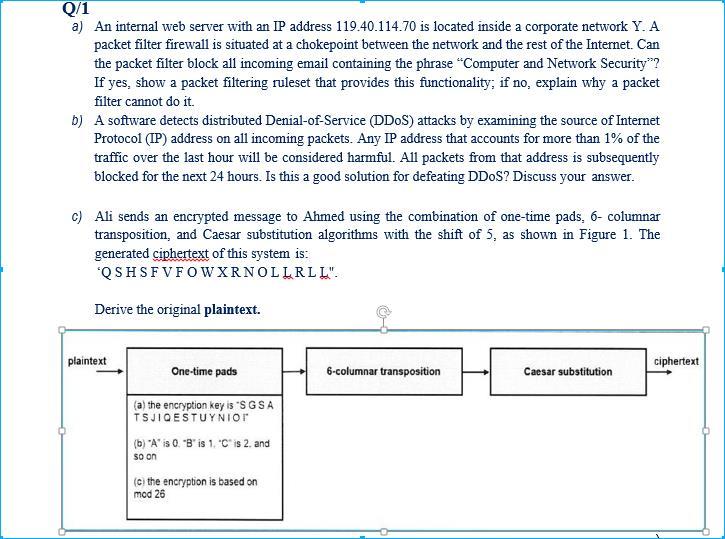
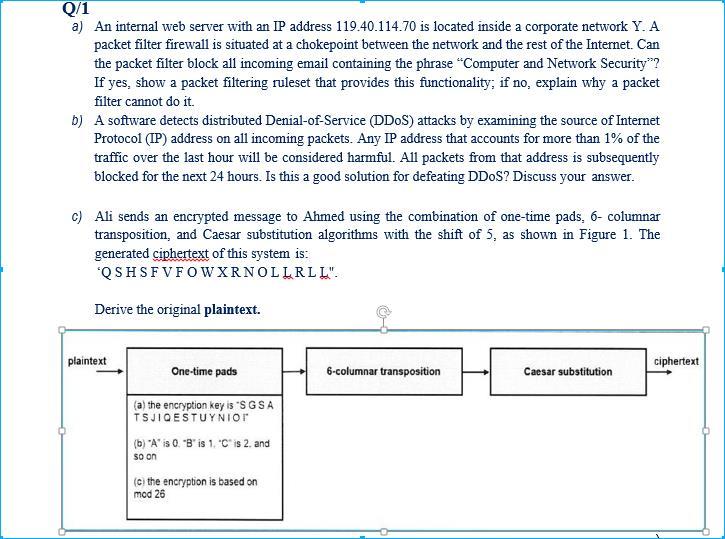
Q/1 a) An internal web server with an IP address 119.40.114.70 is located inside a corporate network Y. A packet filter firewall is situated at a chokepoint between the network and the rest of the Internet. Can the packet filter block all incoming email containing the phrase "Computer and Network Security? If yes, show a packet filtering ruleset that provides this functionality, if no, explain why a packet filter cannot do it. b) A software detects distributed Denial-of-Service (DDoS) attacks by examining the source of Internet Protocol (IP) address on all incoming packets. Any IP address that accounts for more than 1% of the traffic over the last hour will be considered harmful. All packets from that address is subsequently blocked for the next 24 hours. Is this a good solution for defeating DDoS? Discuss your answer. c) Ali sends an encrypted message to Ahmed using the combination of one-time pads, 6- columnar transposition, and Caesar substitution algorithms with the shift of 5, as shown in Figure 1. The generated ciphertext of this system is: 'QSHSF V FOW XRNOLLRLL". Derive the original plaintext. plaintext ciphertext One-time pads 6-columnar transposition Caesar substitution (a) the encryption key is 'SGSA TSJIQESTUYNIOR (b) "A" is 0. 'B' is 1. Cis 2. and so on (Cthe encryption is based on mod 26 Q/1 a) An internal web server with an IP address 119.40.114.70 is located inside a corporate network Y. A packet filter firewall is situated at a chokepoint between the network and the rest of the Internet. Can the packet filter block all incoming email containing the phrase "Computer and Network Security? If yes, show a packet filtering ruleset that provides this functionality, if no, explain why a packet filter cannot do it. b) A software detects distributed Denial-of-Service (DDoS) attacks by examining the source of Internet Protocol (IP) address on all incoming packets. Any IP address that accounts for more than 1% of the traffic over the last hour will be considered harmful. All packets from that address is subsequently blocked for the next 24 hours. Is this a good solution for defeating DDoS? Discuss your answer. c) Ali sends an encrypted message to Ahmed using the combination of one-time pads, 6- columnar transposition, and Caesar substitution algorithms with the shift of 5, as shown in Figure 1. The generated ciphertext of this system is: 'QSHSF V FOW XRNOLLRLL". Derive the original plaintext. plaintext ciphertext One-time pads 6-columnar transposition Caesar substitution (a) the encryption key is 'SGSA TSJIQESTUYNIOR (b) "A" is 0. 'B' is 1. Cis 2. and so on (Cthe encryption is based on mod 26