Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Q5) consider the following code: int bar(){ char buff[8]; gets(buff); return 0; If the stack of bar before gets is called is: Some data (Ox12345678)
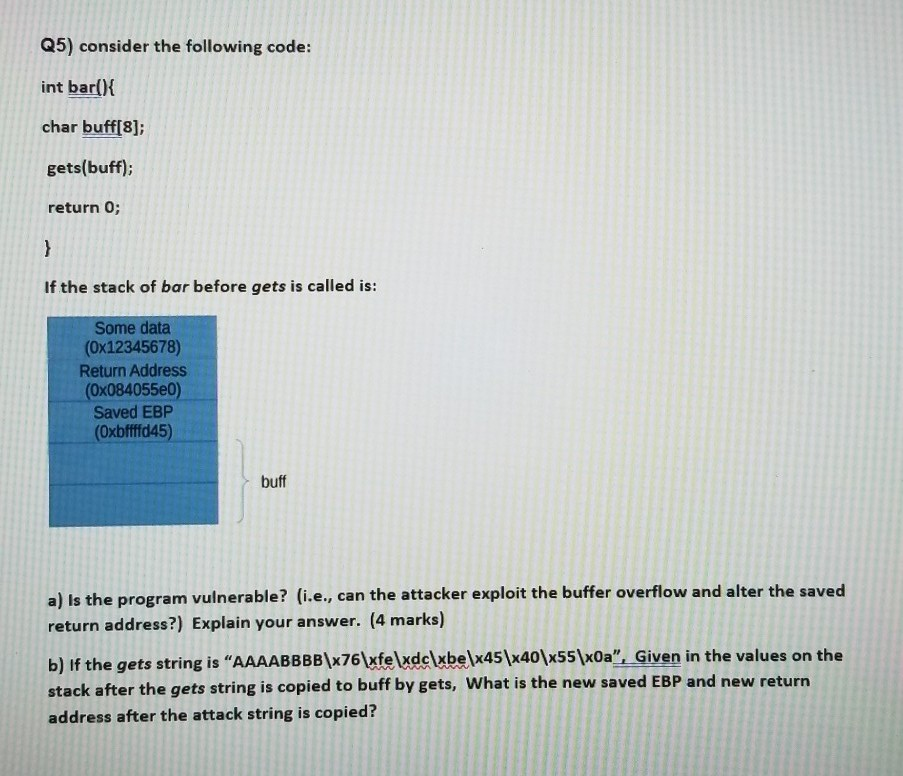
Q5) consider the following code: int bar(){ char buff[8]; gets(buff); return 0; If the stack of bar before gets is called is: Some data (Ox12345678) Return Address (Ox084055e0) Saved EBP (Oxbffffd45) buff a) is the program vulnerable? (i.e., can the attacker exploit the buffer overflow and alter the saved return address?) Explain your answer. (4 marks) b) If the gets string is AAAABBBB\x76\xfe\xdcxbe\x45\x40\x55\xOa". Given in the values on the stack after the gets string is copied to buff by gets, What is the new saved EBP and new return address after the attack string is copied
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


