Answered step by step
Verified Expert Solution
Question
1 Approved Answer
QUESTION 24 White-hat hackers are also called: O Black-hat hackers O Ethical hackers O Thrill-seeker hackers O Crackers QUESTION 25 What is an exact copy
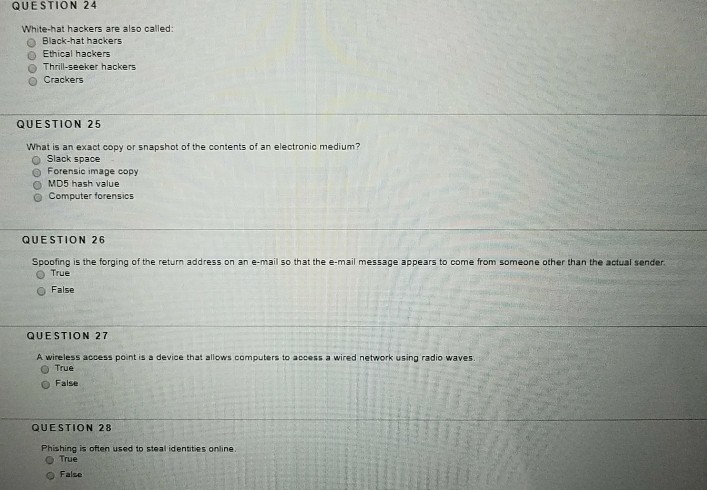
QUESTION 24 White-hat hackers are also called: O Black-hat hackers O Ethical hackers O Thrill-seeker hackers O Crackers QUESTION 25 What is an exact copy or snapshot of the contents of an electronic medium? O Slack space e Forensic image copy O MD5 hash value O Computer forensics QUESTION 26 Spoofing is the forging of the return address on an e-mail so that the e-mail message appears to come from someone other than the actual sender O True O False QUESTION 27 A wireless access point is a device that allows.computers to access a wired network using radio waves O True O False QUESTION 28 Phishing is often used to steal identities online. o True O False
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started