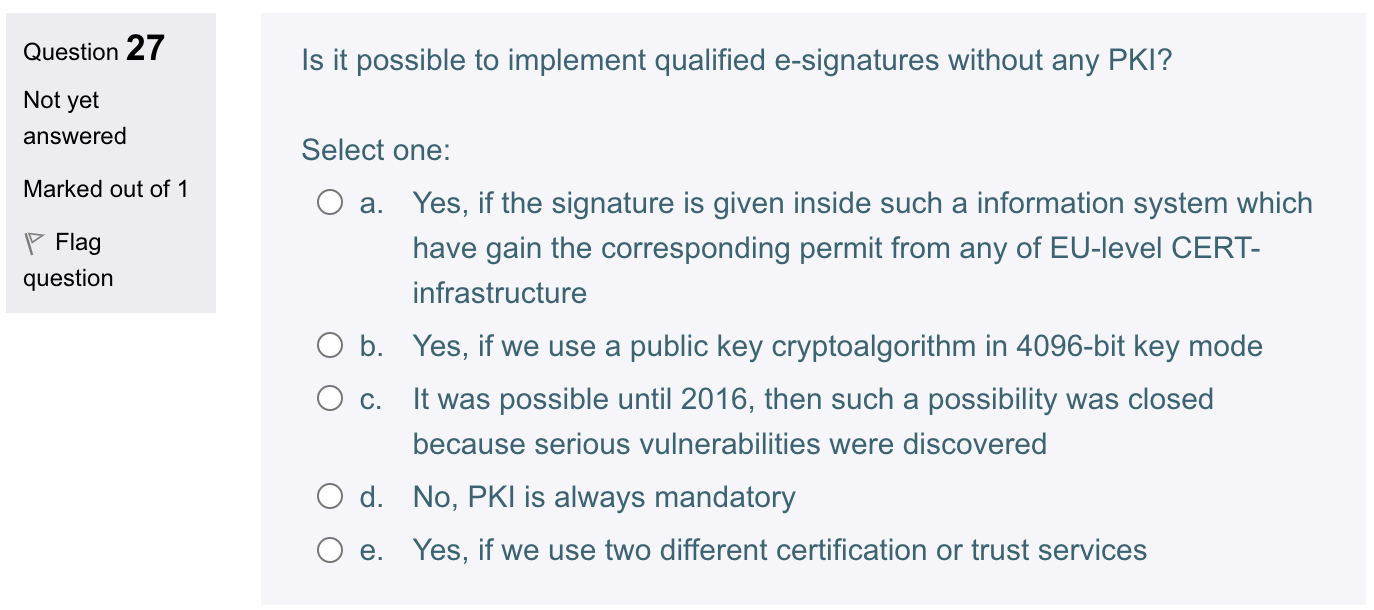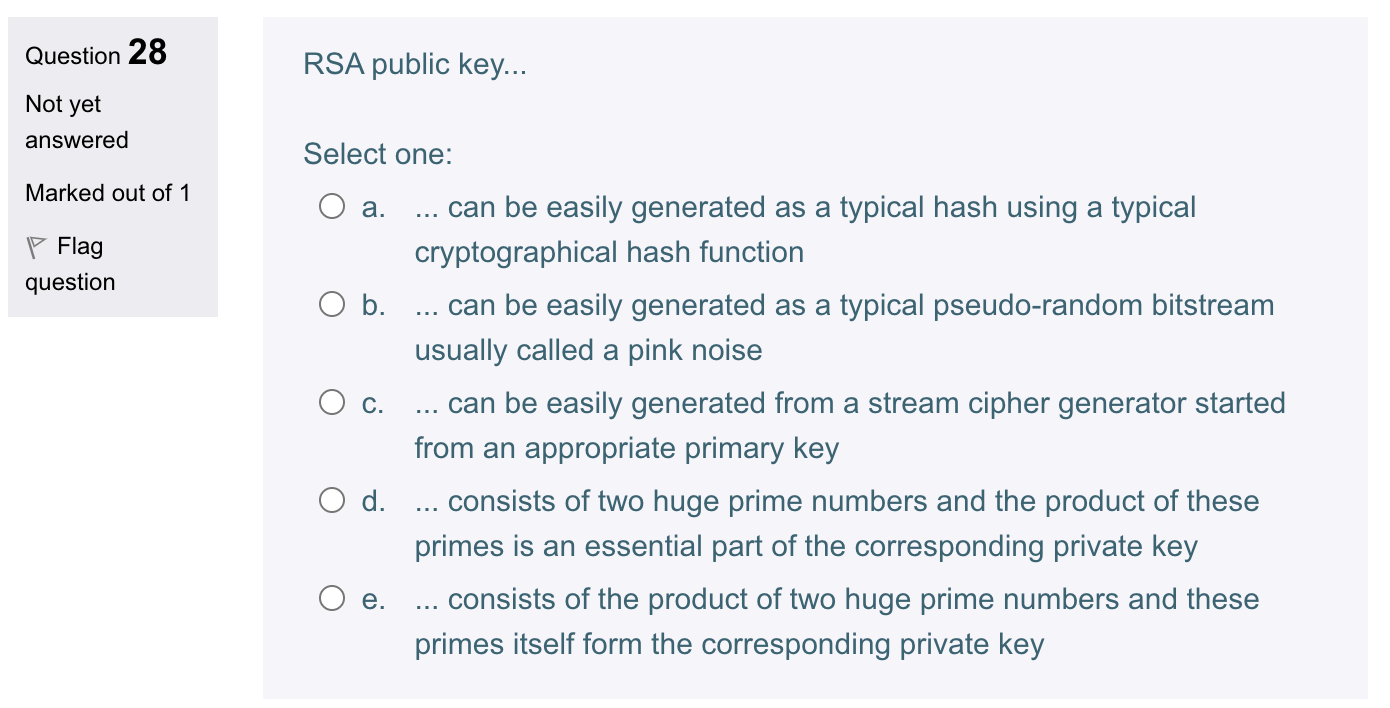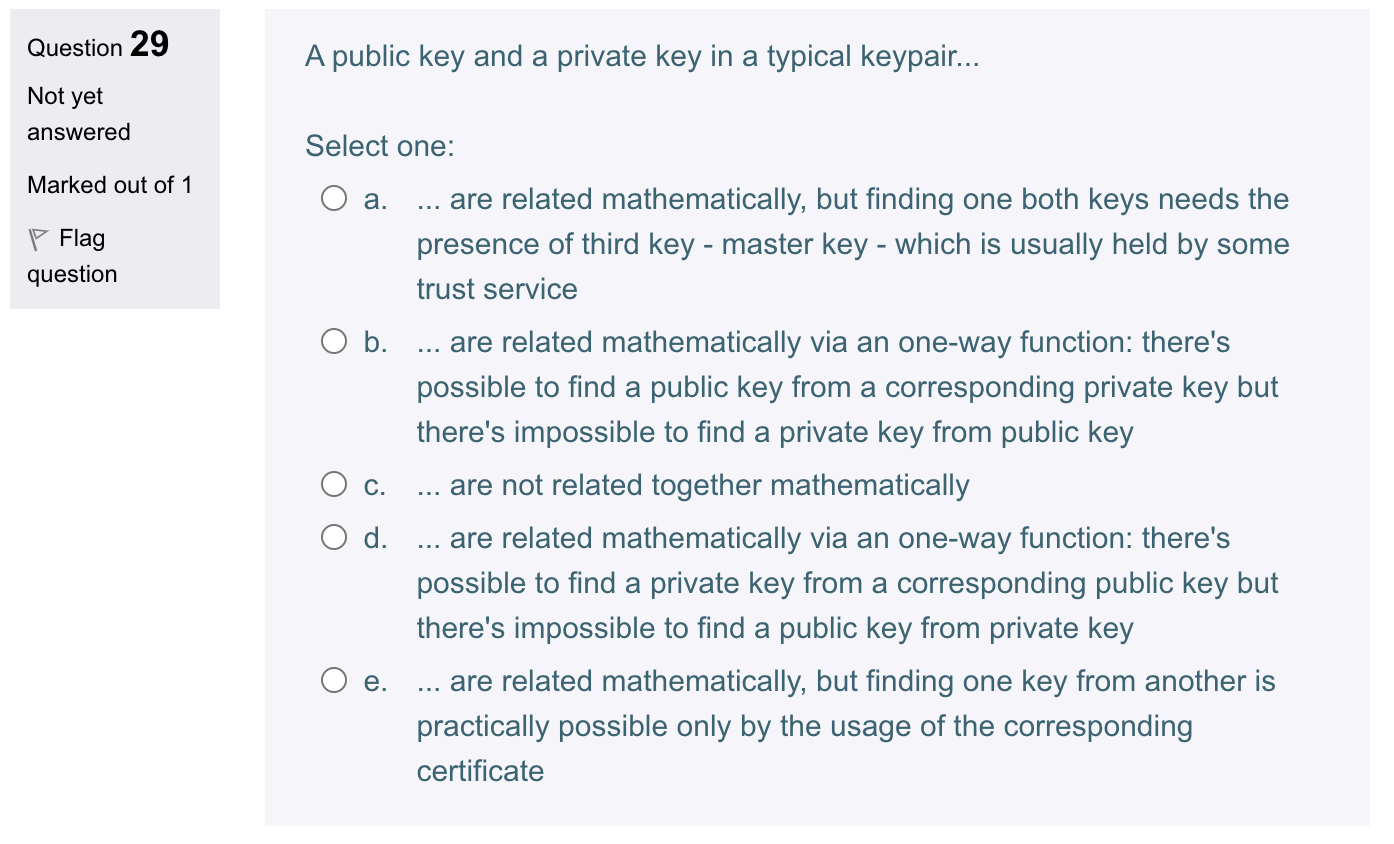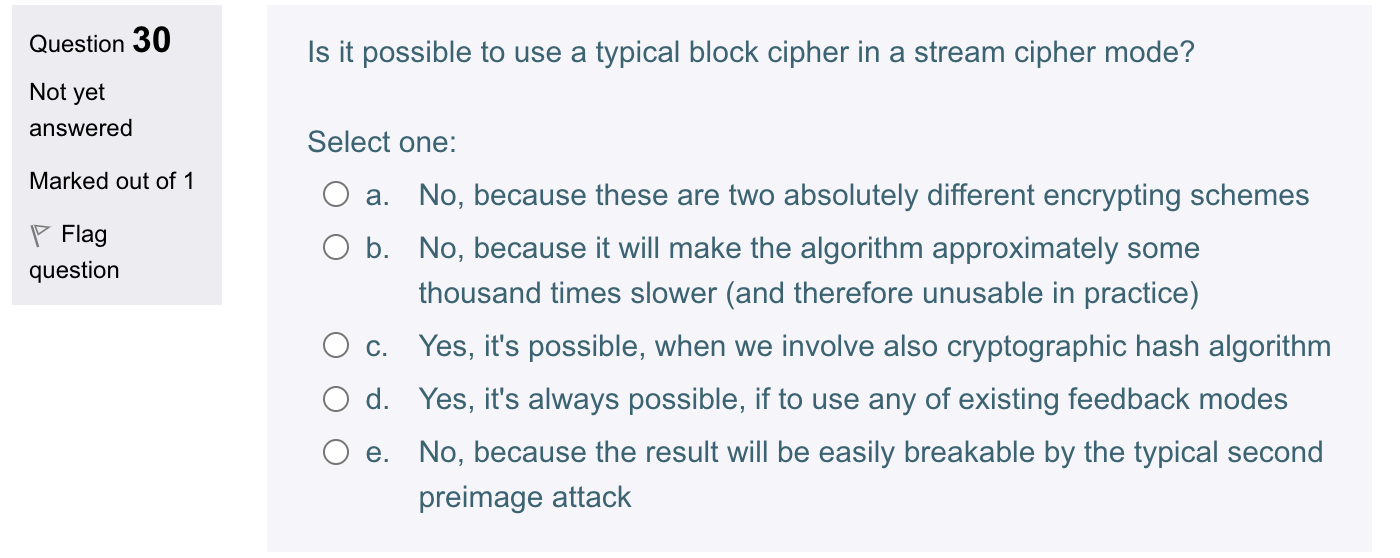
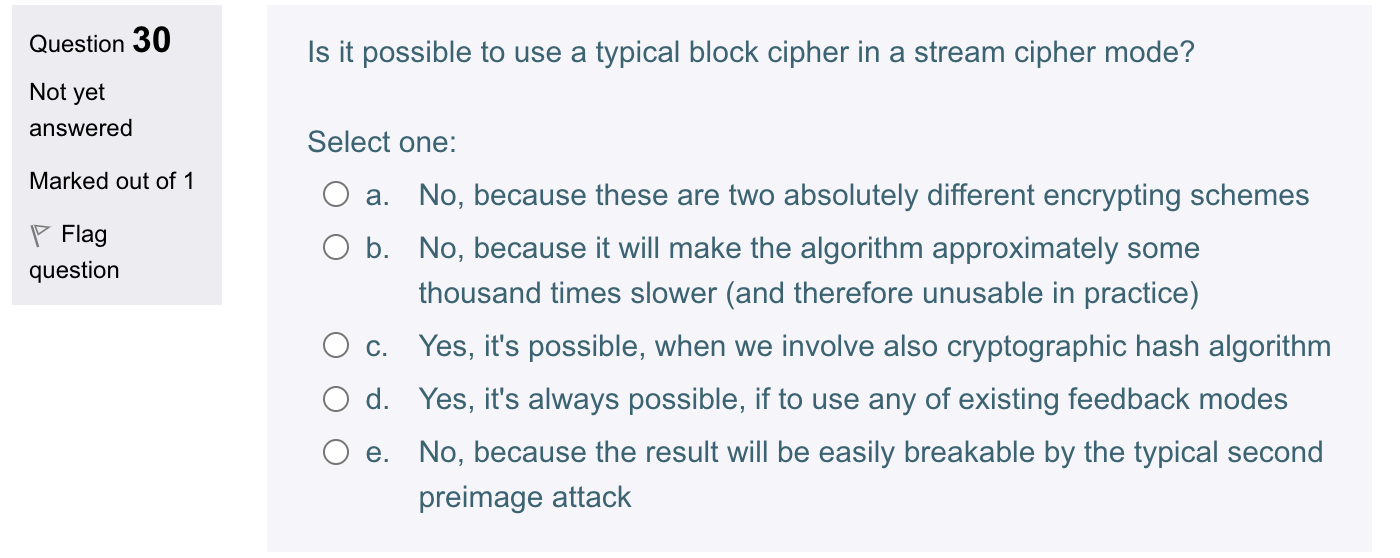
Question 27 Is it possible to implement qualified e-signatures without any PKI ? Not yet answered Select one: Marked out of 1 a. Yes, if the signature is given inside such a information system which have gain the corresponding permit from any of EU-level CERTinfrastructure b. Yes, if we use a public key cryptoalgorithm in 4096-bit key mode c. It was possible until 2016 , then such a possibility was closed because serious vulnerabilities were discovered d. No, PKI is always mandatory e. Yes, if we use two different certification or trust services Question 28 RSA public key... Not yet answered Select one: Marked out of 1 a. ... can be easily generated as a typical hash using a typical cryptographical hash function b. ... can be easily generated as a typical pseudo-random bitstream usually called a pink noise c. ... can be easily generated from a stream cipher generator started from an appropriate primary key d. ... consists of two huge prime numbers and the product of these primes is an essential part of the corresponding private key e. ... consists of the product of two huge prime numbers and these primes itself form the corresponding private key Question 29 A public key and a private key in a typical keypair... Not yet answered Select one: Marked out of 1 a. ... are related mathematically, but finding one both keys needs the presence of third key - master key - which is usually held by some trust service b. ... are related mathematically via an one-way function: there's possible to find a public key from a corresponding private key but there's impossible to find a private key from public key c. are not related together mathematically d. ... are related mathematically via an one-way function: there's possible to find a private key from a corresponding public key but there's impossible to find a public key from private key e. are related mathematically, but finding one key from another is practically possible only by the usage of the corresponding certificate Question 30 Is it possible to use a typical block cipher in a stream cipher mode? Not yet answered Select one: Marked out of 1 a. No, because these are two absolutely different encrypting schemes b. No, because it will make the algorithm approximately some thousand times slower (and therefore unusable in practice) c. Yes, it's possible, when we involve also cryptographic hash algorithm d. Yes, it's always possible, if to use any of existing feedback modes e. No, because the result will be easily breakable by the typical second preimage attack