Question: Question 3 Security Protocols (a) Recall the Dolev-Yao attacker model as discussed in the lecture. Now consider a protocol using outdated cryptographic primitives for encryption
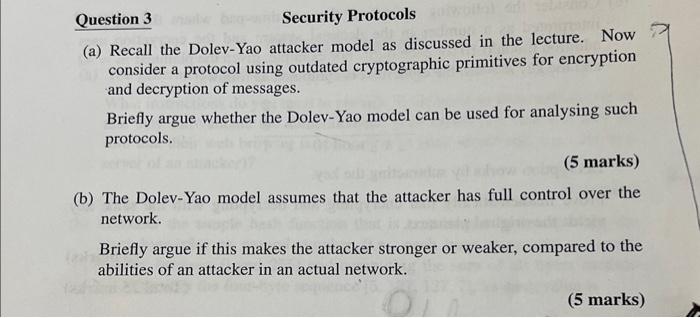
Question 3 Security Protocols (a) Recall the Dolev-Yao attacker model as discussed in the lecture. Now consider a protocol using outdated cryptographic primitives for encryption and decryption of messages. Briefly argue whether the Dolev-Yao model can be used for analysing such protocols. (5 marks) (b) The Dolev-Yao model assumes that the attacker has full control over the network. Briefly argue if this makes the attacker stronger or weaker, compared to the abilities of an attacker in an actual network
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


