Answered step by step
Verified Expert Solution
Question
1 Approved Answer
QUESTION 4 When used for network defense, visualization and monitoring tools are for O checking the network topology O identifying an attack O fixing vulnerabilities
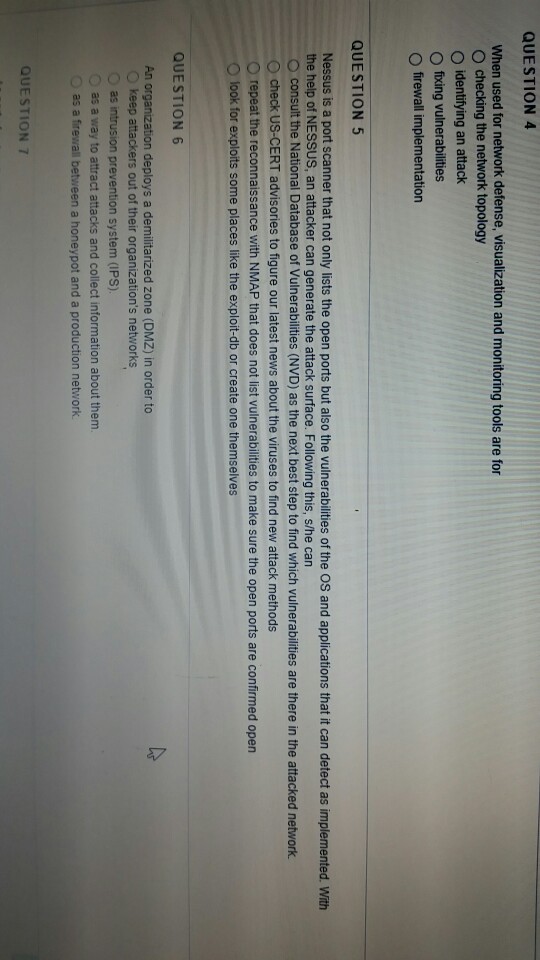
QUESTION 4 When used for network defense, visualization and monitoring tools are for O checking the network topology O identifying an attack O fixing vulnerabilities O firewall implementation QUESTION 5 Nessus is a port scanner that not only lists the open ports but also the vulnerabilities of the OS and applications that it can detect as implemented. With the help of NESSUS, an attacker can generate the attack surface. Following this, s/he can o consult the National Database of Vulnerabilities (NVD) as the next best step to find which vulnerabilities are there in the attacked network O check US-CERT advisories to figure our latest news about the viruses to find new attack methods O repeat the reconnaissance with NMAP that does not list vulnerabilities to make sure the open ports are confirmed open look for exploits some places like the exploit-db or create one themselves QUESTION 6 An organization deploys a demilitarized zone (DMZ) in order to O keep attackers out of their organization's networks O as intrusion prevention system (IPS) as a way to attract attacks and collect information about them as a firewall between a honeypot and a production network QUESTION 7
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started