Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Question 7 2 Points Bob is encrypting his disk drive using a one time pad. His data is stored and encrypted in chunks on the
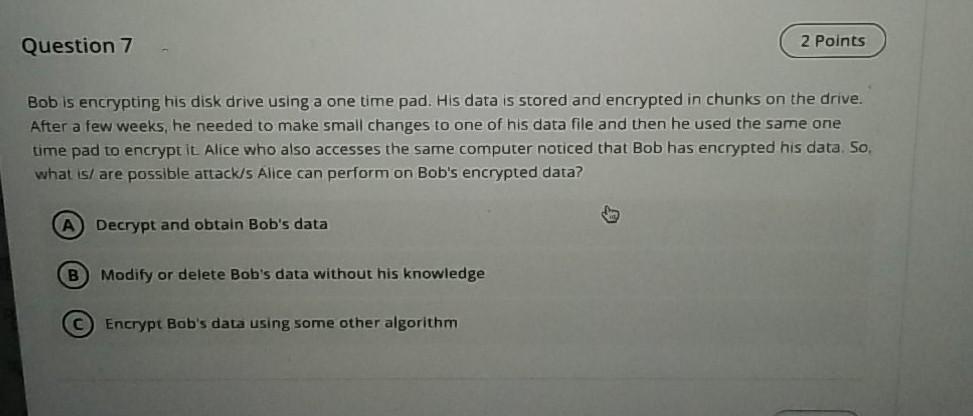
Question 7 2 Points Bob is encrypting his disk drive using a one time pad. His data is stored and encrypted in chunks on the drive. After a few weeks, he needed to make small changes to one of his data file and then he used the same one time pad to encrypt It Alice who also accesses the same computer noticed that Bob has encrypted his data. So, what is/are possible attacks Alice can perform on Bob's encrypted data? A Decrypt and obtain Bob's data B Modify or delete Bob's data without his knowledge C Encrypt Bob's data using some other algorithm
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


