Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Rivier University I N . . . Mail - Nimmagadda... Paraphrasing Toc Security ( Jan ) home > and prevention systems ( NIDS / NIPS
Rivier University I N
Mail Nimmagadda...
Paraphrasing Toc
Security Jan home
and prevention systems NIDSNIPS
cxzcy
Jump to level
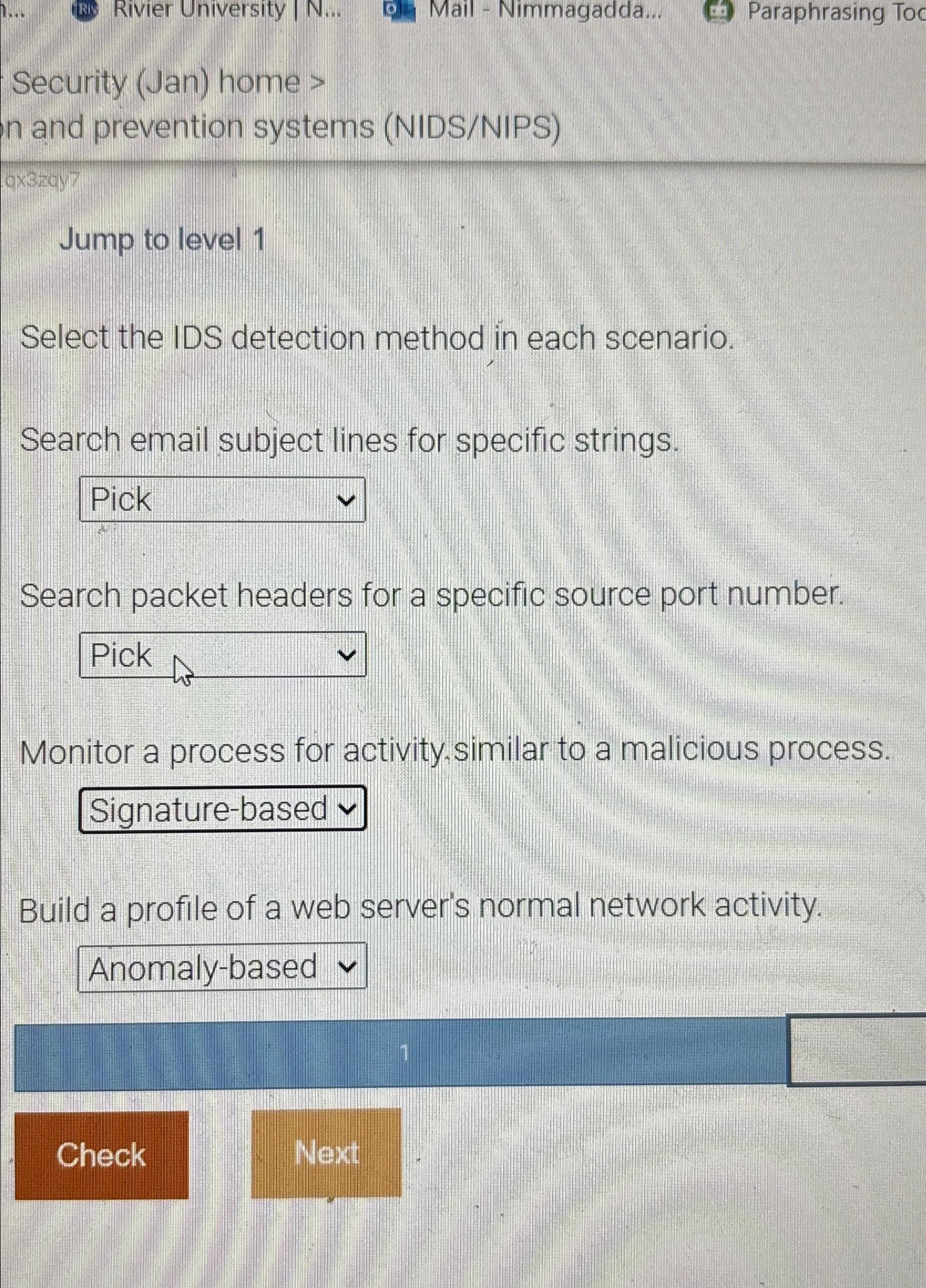
Select the IDS detection method in each scenario.
Search email subject lines for specific strings.
Search packet headers for a specific source port number.
Monitor a process for activity.similar to a malicious process.
Build a profile of a web server's normal network activity.
Check
Next
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


