Answered step by step
Verified Expert Solution
Question
1 Approved Answer
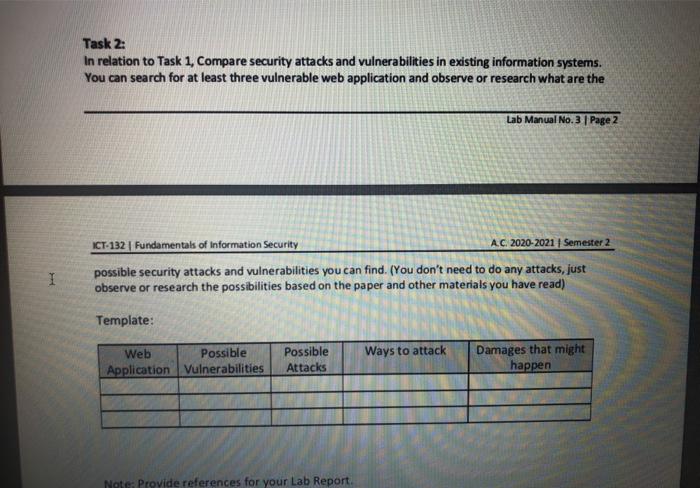
Task 2: In relation to Task 1, Compare security attacks and vulnerabilities in existing information systems. You can search for at least three vulnerable web
Task 2: In relation to Task 1, Compare security attacks and vulnerabilities in existing information systems. You can search for at least three vulnerable web application and observe or research what are the Lab Manual No. 3 | Page 2 ICT-132 | Fundamentals of Information Security A.C. 2020-2021 | Semester 2 possible security attacks and vulnerabilities you can find. (You don't need to do any attacks, just observe or research the possibilities based on the paper and other materials you have read) Template: Web Possible Damages that might happen Possible Ways to attack Application Vulnerabilities Attacks
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started