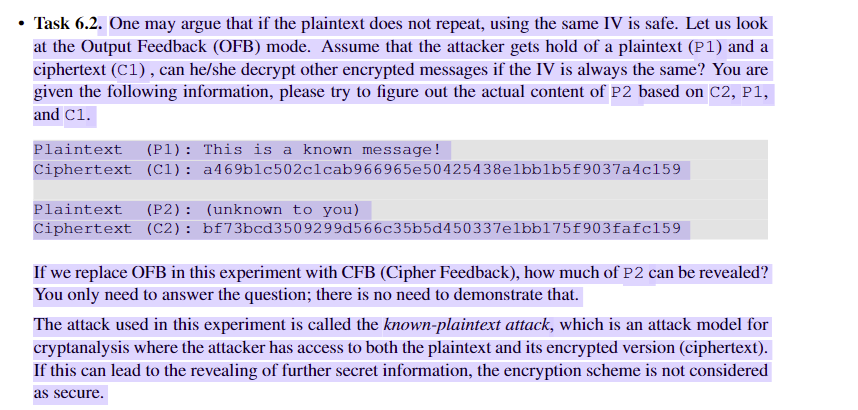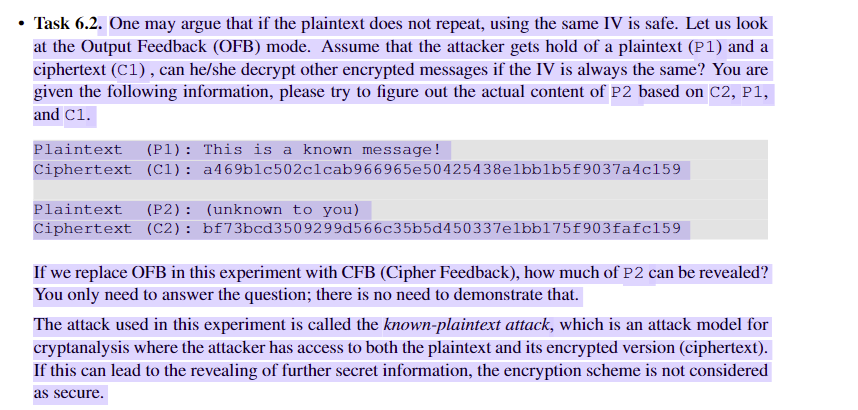
. Task 6.2. One may argue that if the plaintext does not repeat, using the same IV is safe. Let us look at the Output Feedback (OFB) mode. Assume that the attacker gets hold of a plaintext (P1) and a ciphertext (C1), can he/she decrypt other encrypted messages if the IV is always the same? You are given the following information, please try to figure out the actual content of P2 based on C2, P1, and C1. Plaintext (P1): This is a known message! Ciphertext (C1): a469blc502c1cab966965e50425438e1bblb5f9037a4c159 Plaintext (P2): (unknown to you) Ciphertext (C2): bf73bcd3509299d566c35b5d450337e1bb175f903fafc159 If we replace OFB in this experiment with CFB (Cipher Feedback), how much of P2 can be revealed? You only need to answer the question; there is no need to demonstrate that. The attack used in this experiment is called the known-plaintext attack, which is an attack model for cryptanalysis where the attacker has access to both the plaintext and its encrypted version (ciphertext) If this can lead to the revealing of further secret information, the encryption scheme is not considered as secure . Task 6.2. One may argue that if the plaintext does not repeat, using the same IV is safe. Let us look at the Output Feedback (OFB) mode. Assume that the attacker gets hold of a plaintext (P1) and a ciphertext (C1), can he/she decrypt other encrypted messages if the IV is always the same? You are given the following information, please try to figure out the actual content of P2 based on C2, P1, and C1. Plaintext (P1): This is a known message! Ciphertext (C1): a469blc502c1cab966965e50425438e1bblb5f9037a4c159 Plaintext (P2): (unknown to you) Ciphertext (C2): bf73bcd3509299d566c35b5d450337e1bb175f903fafc159 If we replace OFB in this experiment with CFB (Cipher Feedback), how much of P2 can be revealed? You only need to answer the question; there is no need to demonstrate that. The attack used in this experiment is called the known-plaintext attack, which is an attack model for cryptanalysis where the attacker has access to both the plaintext and its encrypted version (ciphertext) If this can lead to the revealing of further secret information, the encryption scheme is not considered as secure