Question
Task Overview PCAP FILE- https://github.com/ACandeias/IntrusionDetection/tree/master/PCAP This lab is intended to be run in a Linux virtual machine that has the program Wireshark installed at Security
Task Overview
PCAP FILE- https://github.com/ACandeias/IntrusionDetection/tree/master/PCAP
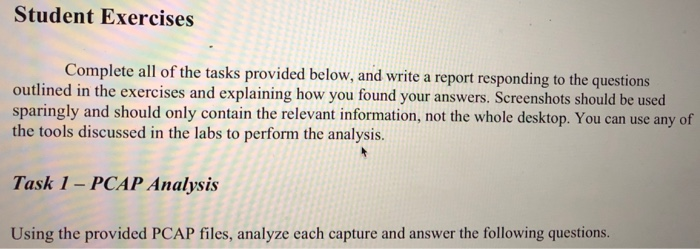
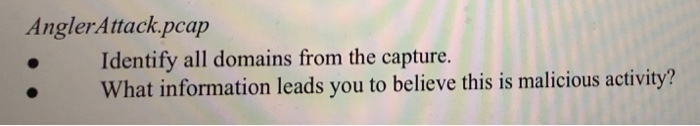
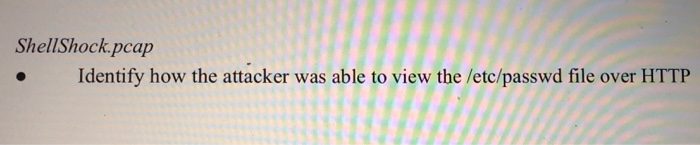
This lab is intended to be run in a Linux virtual machine that has the program Wireshark installed at Security Onion.The students will practice using the tools Wireshark, Tshark, and NetMiner to analyze packets captured during different attack scenarios. They will use their knowledge of network protocols to evaluate what happened in the attacks and extract important data from the captured traffic. Additionally, students will be introduced to setting up Access Control Lists (ACLs) using the IPTables tool.The program comes pre-installed in the SecurityOnion VM. To start it, open the start menu in the top left corner and go to Security Onion > NetworkMiner, and the program will open to empty analysis panes. In the menu options of the program, select File > Open > IntrusionDetection > PCAP in order to choose a PCAP file to open.
Dropbox link for the actual question- https://www.dropbox.com/s/96z2w69yz3am7w4/Lab3-Advanced%20Packet%20Analysis.pdf?dl=0
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started