Question
The affine cipher is a substitution cipher, where a plaintext letter x is enciphered into a ciphertext letter y as follows: x y = x
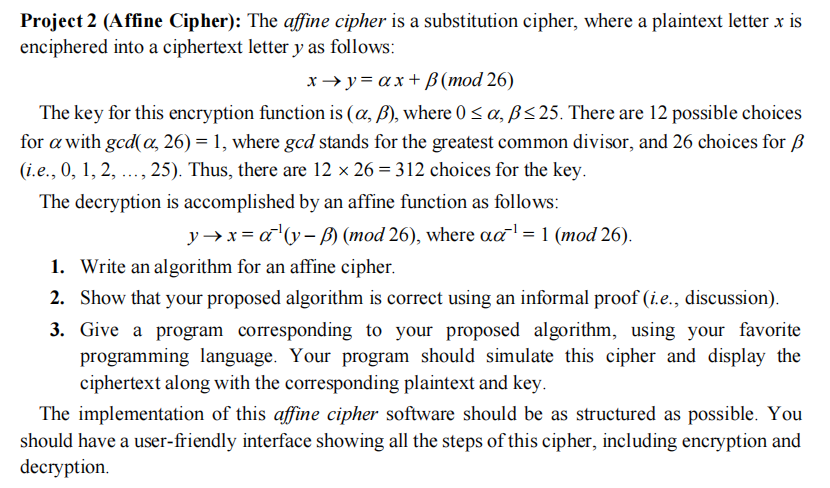 The affine cipher is a substitution cipher, where a plaintext letter x is enciphered into a ciphertext letter y as follows: x y = x + (mod 26) The key for this encryption function is (, ), where 0 , 25. There are 12 possible choices for with gcd(, 26) = 1, where gcd stands for the greatest common divisor, and 26 choices for (i.e., 0, 1, 2, , 25). Thus, there are 12 26 = 312 choices for the key. The decryption is accomplished by an affine function as follows: y x = 1(y ) (mod 26), where 1 = 1 (mod 26). 1. Write an algorithm for an affine cipher. 2. Show that your proposed algorithm is correct using an informal proof (i.e., discussion). 3. Give a program corresponding to your proposed algorithm, using your favorite programming language. Your program should simulate this cipher and display the ciphertext along with the corresponding plaintext and key. The implementation of this affine cipher software should be as structured as possible. You should have a user-friendly interface showing all the steps of this cipher, including encryption and decryption.
The affine cipher is a substitution cipher, where a plaintext letter x is enciphered into a ciphertext letter y as follows: x y = x + (mod 26) The key for this encryption function is (, ), where 0 , 25. There are 12 possible choices for with gcd(, 26) = 1, where gcd stands for the greatest common divisor, and 26 choices for (i.e., 0, 1, 2, , 25). Thus, there are 12 26 = 312 choices for the key. The decryption is accomplished by an affine function as follows: y x = 1(y ) (mod 26), where 1 = 1 (mod 26). 1. Write an algorithm for an affine cipher. 2. Show that your proposed algorithm is correct using an informal proof (i.e., discussion). 3. Give a program corresponding to your proposed algorithm, using your favorite programming language. Your program should simulate this cipher and display the ciphertext along with the corresponding plaintext and key. The implementation of this affine cipher software should be as structured as possible. You should have a user-friendly interface showing all the steps of this cipher, including encryption and decryption.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started