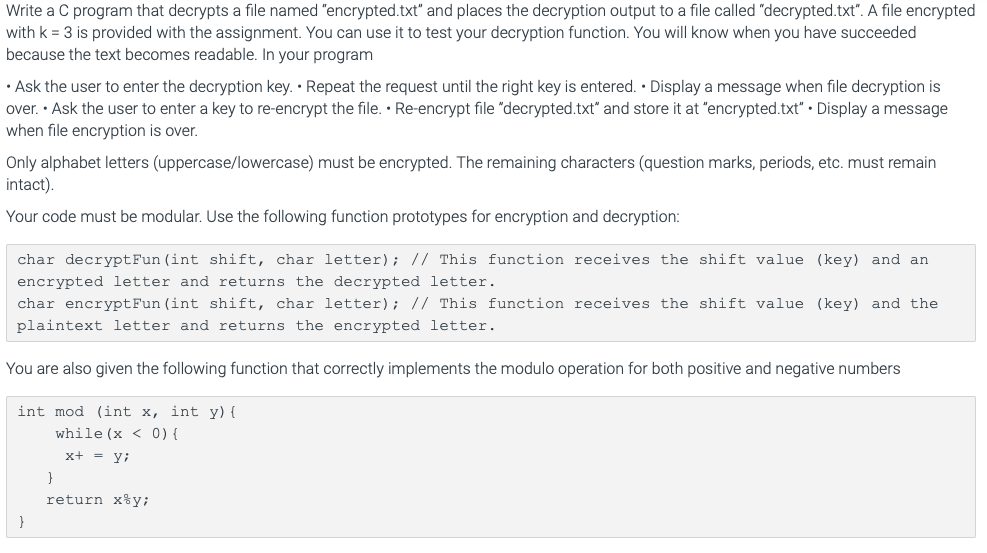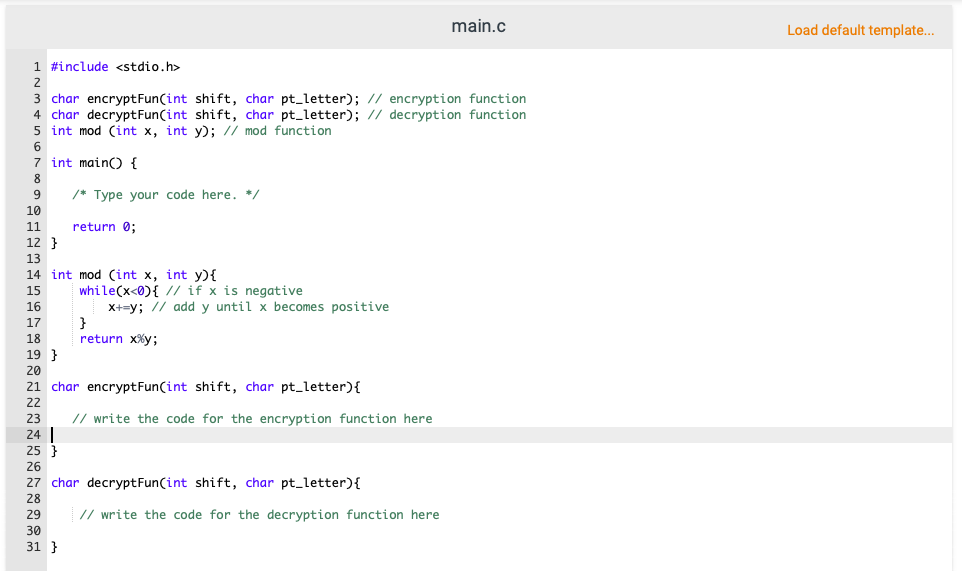

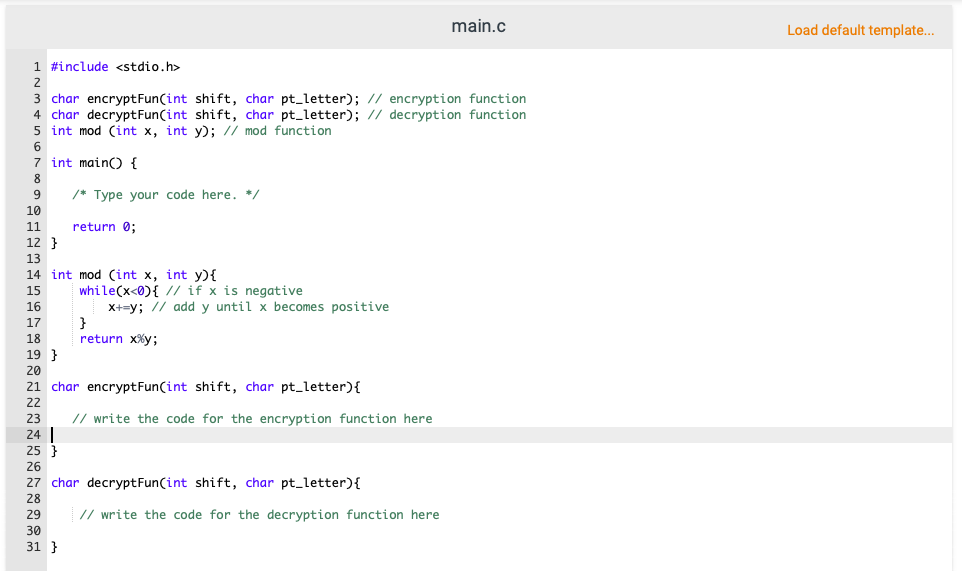
The Caesar's cipher is a cryptographic method for encrypting text such that it becomes unreadable to a party without access to the cryptographic key. It is named after Julius Caesar, who allegedly used it to protect messages of military significance. The encryption and decryption operations are simple shifts of the alphabet letters in a cyclic fashion. Mathematically, for a key k, the encryption and decryption are defined as: Encryption: C=(x+k) mod 26, Decryption: x=(c-k) mod 26. To illustrate the use of the Ceasar's cipher, consider the encryption of "fry" with key k = 3. Letters f, r, y correspond to the 5th, 16th, and 24th letter of the alphabet (letter 'a' being the oth). f:(5+3) mod 26 = 8-ir:(16+3) mod26 = 19+ y:(24+3) mod 26 = 1 + Similarly, the decryption of i,ub follows the reverse process i:(8-3) mod26 = 5+f u:(19-3) mod26 = 16+ b:(1-3) mod26 = 24 NOTE: The modulo operation for negative numbers is different from the % arithmetic operator in C (look for the code provided at the end). Write a C program that decrypts a file named "encrypted.txt" and places the decryption output to a file called "decrypted.txt". A file encrypted with k = 3 is provided with the assignment. You can use it to test your decryption function. You will know when you have succeeded because the text becomes readable. In your program Ask the user to enter the decryption key.. Repeat the request until the right key is entered. Display a message when file decryption is over. Ask the user to enter a key to re-encrypt the file. Re-encrypt file "decrypted.txt" and store it at "encrypted.txt". Display a message when file encryption is over. Only alphabet letters (uppercase/lowercase) must be encrypted. The remaining characters (question marks, periods, etc. must remain intact) Your code must be modular. Use the following function prototypes for encryption and decryption: char decryptFun (int shift, char letter); // This function receives the shift value (key) and an encrypted letter and returns the decrypted letter. char encryptFun (int shift, char letter); // This function receives the shift value (key) and the plaintext letter and returns the encrypted letter. You are also given the following function that correctly implements the modulo operation for both positive and negative numbers int mod (int x, int y){ while (x 2 3 char encryptFun(int shift, char pt_letter); // encryption function 4 char decryptFun(int shift, char pt_letter); // decryption function 5 int mod (int x, int y); // mod function 6 7 int main() { 8 9 /* Type your code here. */ 10 10 11 return 0; 12 } 13 14 int mod (int x, int y){ 1 while(x