Answered step by step
Verified Expert Solution
Question
1 Approved Answer
The computer frauds that are publicly revealed represent only the tip of the iceberg. Although many people perceive that the major threat to computer security
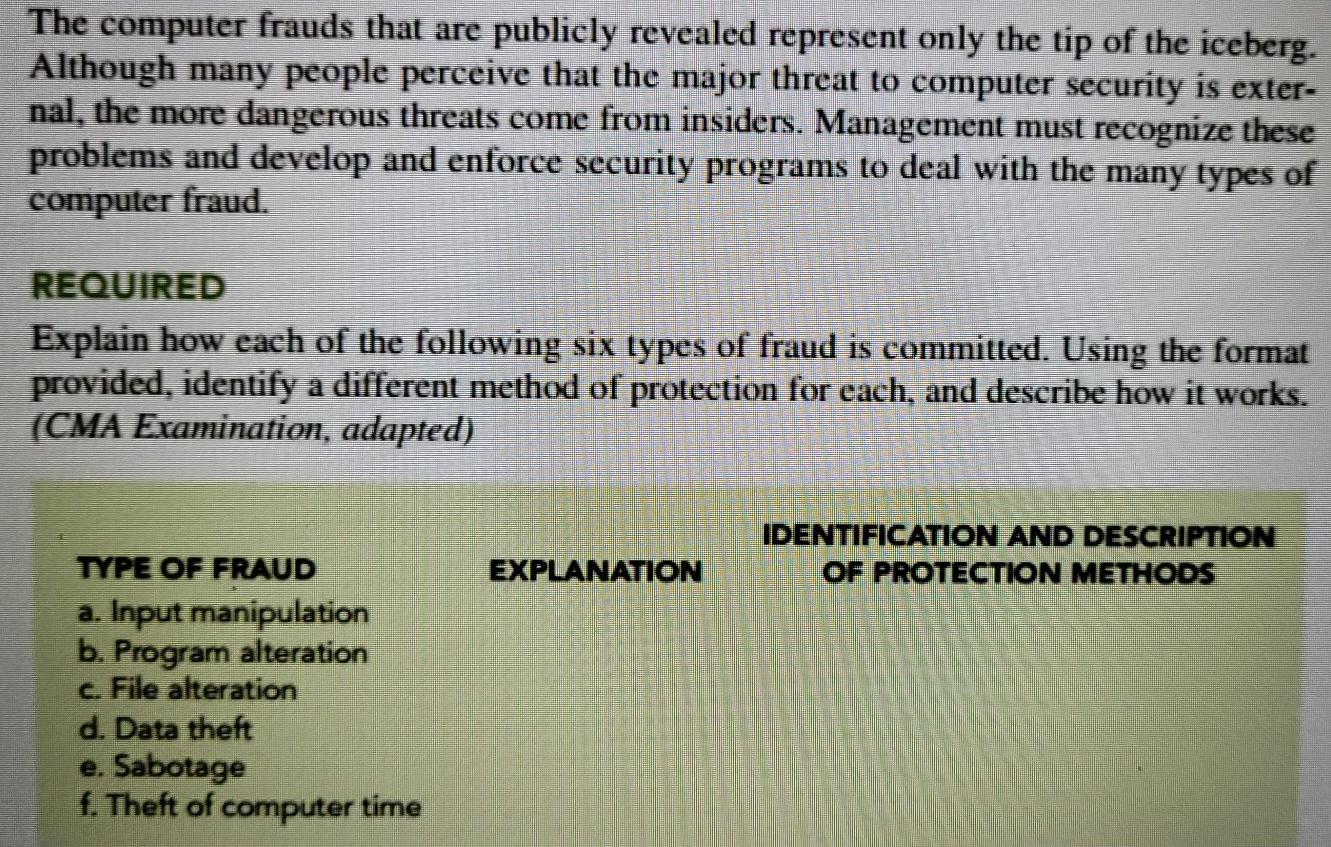
The computer frauds that are publicly revealed represent only the tip of the iceberg. Although many people perceive that the major threat to computer security is exter- nal, the more dangerous threats come from insiders. Management must recognize these problems and develop and enforce security programs to deal with the many types of computer fraud. REQUIRED Explain how each of the following six types of fraud is committed. Using the format provided, identify a different method of protection for cach, and describe how it works. (CMA Examination, adapted) IDENTIFICATION AND DESCRIPTION OF PROTECTION METHODS EXPLANATION TYPE OF FRAUD a. Input manipulation b. Program alteration C. File alteration d. Data theft e. Sabotage f. Theft of computer time
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started