Answered step by step
Verified Expert Solution
Question
1 Approved Answer
This is a cryptology question from the book Introduction to Modern Cryptology by Katz and Lindell. 3. Let F be a pseudorandom function and G
This is a cryptology question from the book Introduction to Modern Cryptology by Katz and Lindell. 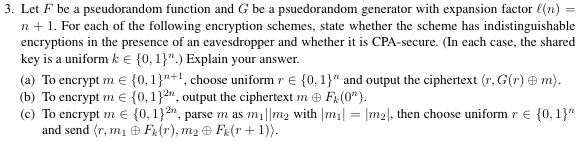
3. Let F be a pseudorandom function and G be a psuedrandom generator with expansion factor E n) 3. Let F be a pseudorandom function and G be a psuedorandom generator with expansion factor (n) n +1. For each of the following encryption schemes, state whether the scheme has indistinguishable encryptions in the presence of an eavesdropper and whether it is CPA-secure. (In each case, the shared key is a uniformke 10,1 key is a uniform k e 0, 1 Explain your answer (a) To encrypt m E {0, 1)"+1, choose uniform r E {0, 1)" and output the ciphertext (r, G(r) m) (b) To encrypt m e { 0, 1 }2n, output the ciphertext m E Fk(0") (c) To encrypt m E 0,12 parse m as milm with mlm2,then choose uniform r E 0,1" parse m as m1 with m and send(r, mi Fk(r). Tn 2 E Fr(r + 1)) 3. Let F be a pseudorandom function and G be a psuedrandom generator with expansion factor E n) 3. Let F be a pseudorandom function and G be a psuedorandom generator with expansion factor (n) n +1. For each of the following encryption schemes, state whether the scheme has indistinguishable encryptions in the presence of an eavesdropper and whether it is CPA-secure. (In each case, the shared key is a uniformke 10,1 key is a uniform k e 0, 1 Explain your answer (a) To encrypt m E {0, 1)"+1, choose uniform r E {0, 1)" and output the ciphertext (r, G(r) m) (b) To encrypt m e { 0, 1 }2n, output the ciphertext m E Fk(0") (c) To encrypt m E 0,12 parse m as milm with mlm2,then choose uniform r E 0,1" parse m as m1 with m and send(r, mi Fk(r). Tn 2 E Fr(r + 1)) 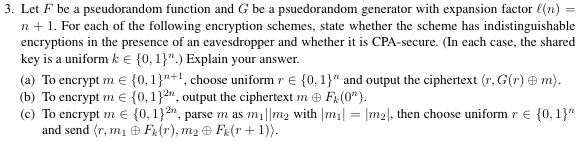
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


