Answered step by step
Verified Expert Solution
Question
1 Approved Answer
this is all they give us to work with PART-01: Programming Exercise In this LAB, you will develop a program to encrypt plaintext text given
this is all they give us to work with
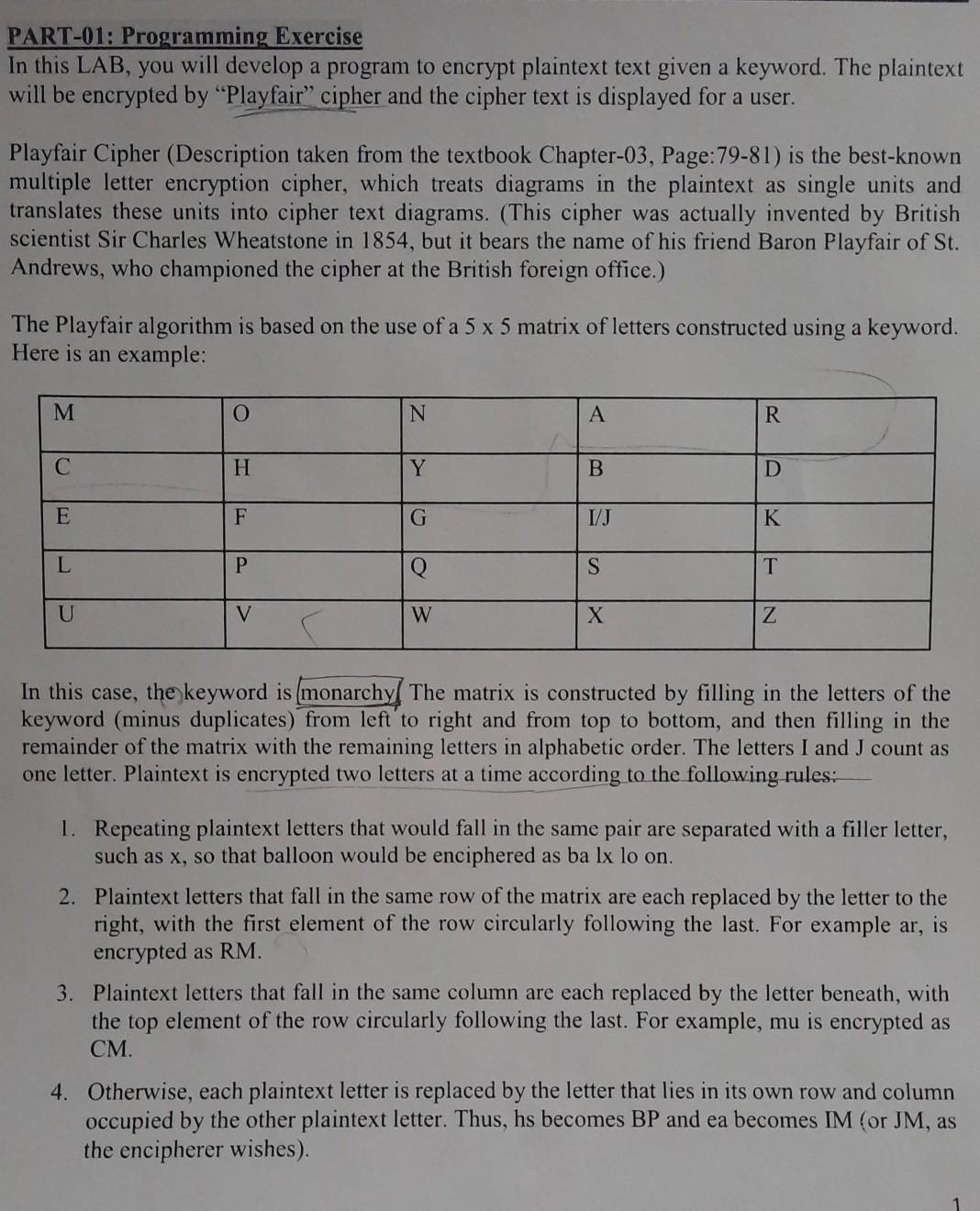
PART-01: Programming Exercise In this LAB, you will develop a program to encrypt plaintext text given a keyword. The plaintext will be encrypted by "Playfair cipher and the cipher text is displayed for a user. Playfair Cipher (Description taken from the textbook Chapter-03, Page:79-81) is the best-known multiple letter encryption cipher, which treats diagrams in the plaintext as single units and translates these units into cipher text diagrams. (This cipher was actually invented by British scientist Sir Charles Wheatstone in 1854, but it bears the name of his friend Baron Playfair of St. Andrews, who championed the cipher at the British foreign office.) The Playfair algorithm is based on the use of a 5 x 5 matrix of letters constructed using a keyword. Here is an example: M O N R H Y B D E F G I/J K L P S T U V W Z In this case, the keyword is (monarchy The matrix is constructed by filling in the letters of the keyword (minus duplicates) from left to right and from top to bottom, and then filling in the remainder of the matrix with the remaining letters in alphabetic order. The letters I and I count as one letter. Plaintext is encrypted two letters at a time according to the following rules: 1. Repeating plaintext letters that would fall in the same pair are separated with a filler letter, such as x, so that balloon would be enciphered as ba lx lo on. 2. Plaintext letters that fall in the same row of the matrix are each replaced by the letter to the right, with the first element of the row circularly following the last. For example ar, is encrypted as RM. 3. Plaintext letters that fall in the same column are each replaced by the letter beneath, with the top element of the row circularly following the last. For example, mu is encrypted as . . 4. Otherwise, each plaintext letter is replaced by the letter that lies in its own row and column occupied by the other plaintext letter. Thus, hs becomes BP and ea becomes IM (or JM, as the encipherer wishes)Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started